10.0 Defender for Endpoint(MDE): Indicator
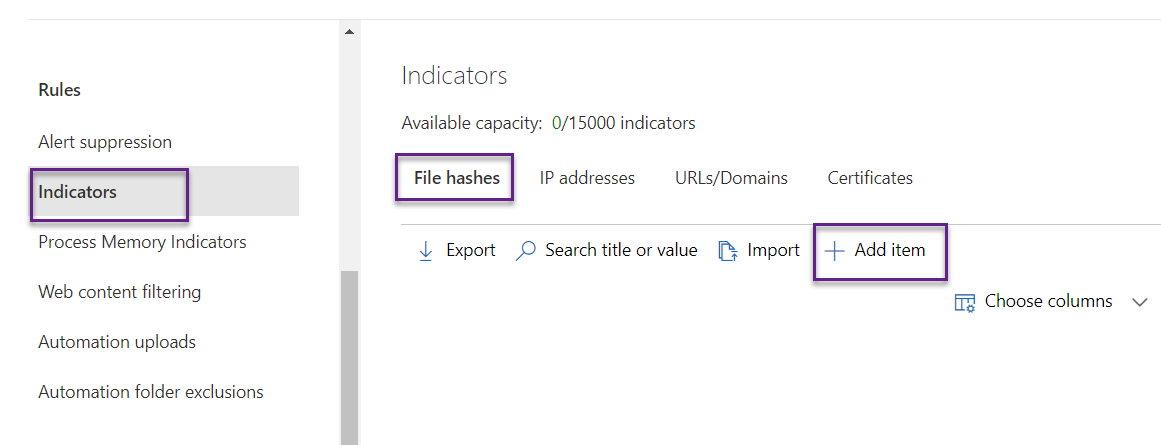
Microsoft Defender for Endpoint has its own intelligence database and based on that it triggers alerts. If we want to trigger alerts based on our own intelligence or we can say IoC that is also possible in MDE. Defender for Endpoint has features called Indicators where we can upload all the intelligence and based on that MDE trigger alert. The intelligence can be in terms of file hashes, IP address, URL/domain, and certificate. We can also upload one item at a time or we can upload in bulk using import.
Navigate to Defender for Endpoint portal(security.microsoft.com), go to Settings->Endpoints->Indicators->Add item. Let's start with File hashes.
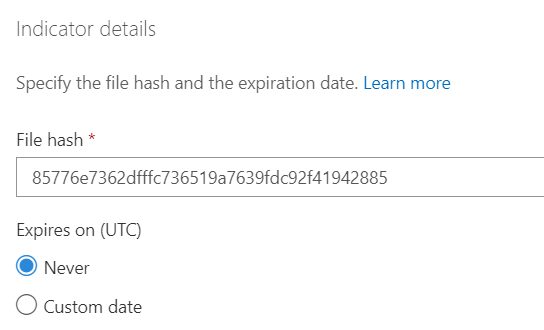
Supply the file that has value that we want to block, and set an expiration date.
On the Action tab, we choose what action MDE should take when it encounters supplied file hash value. We want to block the execution so we have chosen as below.
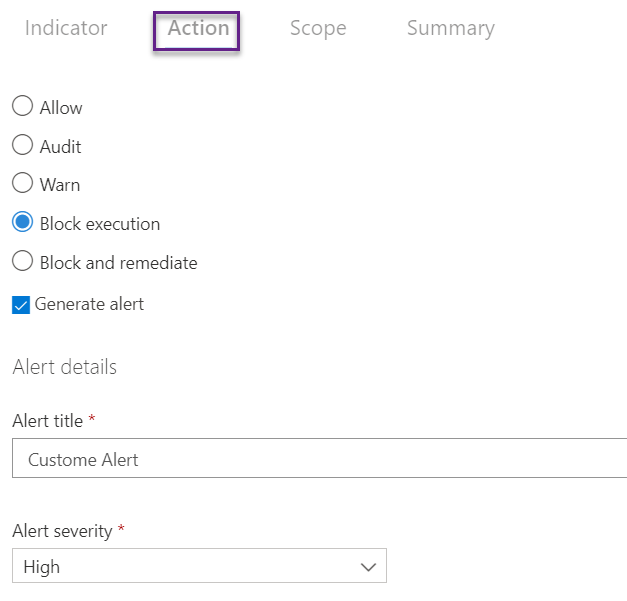
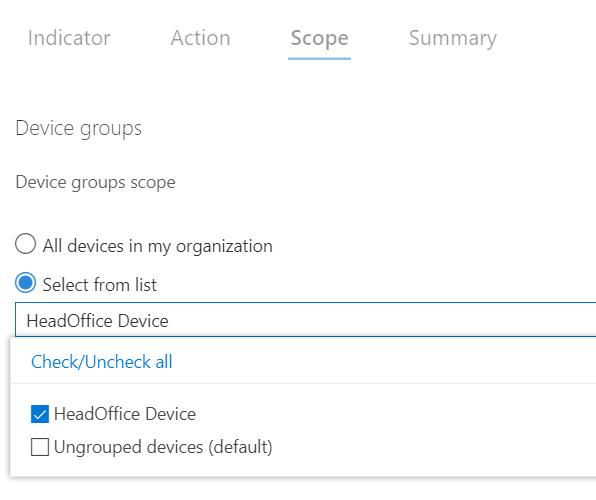
On the scope tab, we have chosen the HeadOffie Device group so we want these settings only to work for devices in the head office.
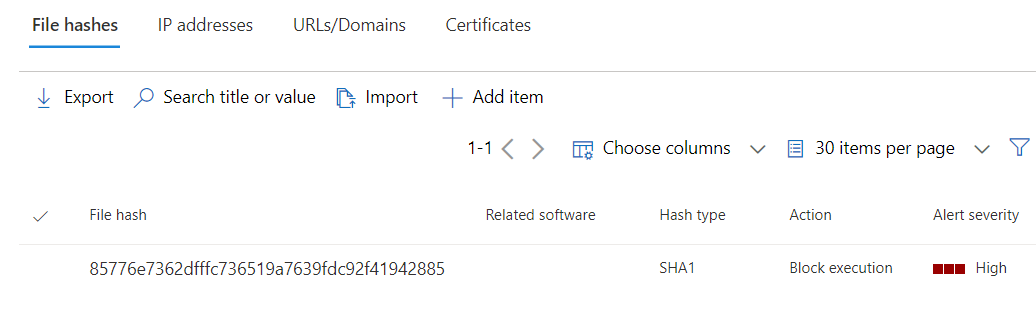
We can see below the indicator has been created and triggered whenever this will be encountered in any of those head office devices.
Bulk Import
Click on Import.
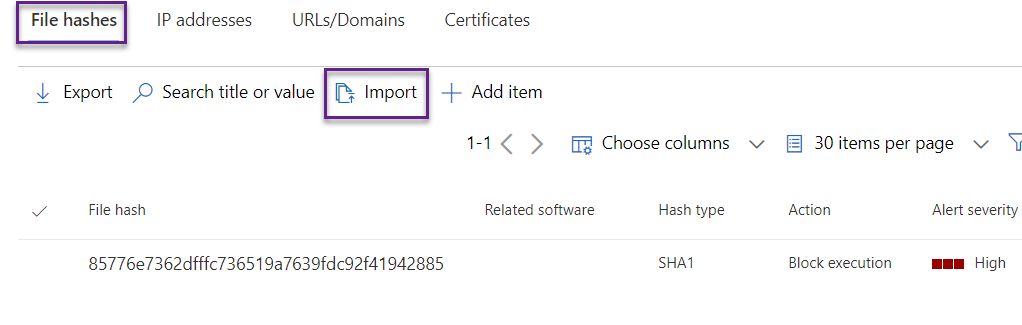
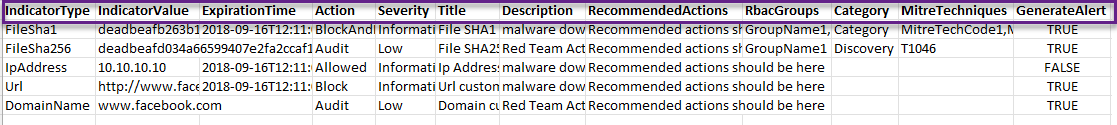
There is a certain format for CSV files that we need to follow. We can download it from here as highlighted. Once downloaded then fill it out and upload.
If we don't follow the same column name then the upload will be failed.
We can also download the sample file from the below link.
In the same way, we can import the other types of indicators.