14.0 Defender for Endpoint(MDE): Custom Detection Rule
Defender for Endpoint detects threats using its own advanced threat intelligence system based on artificial intelligence, machine learning, and behavioral analytics. Based on that intelligence database MDE generates alerts/incidents in case of suspicious activities, or attacks.
We can also generate alerts/incidents based on our own intelligence in MDE. We can define our organization's specific conditions or threats to create the rule. There is a feature called Custom detection rules which provides this capability.
Scenario for custom detection rule
For this lab, we want to trigger the custom detection rule if anybody modified the AV scan exclusion list. Privileged users or bad actors can add/remove/modify the Defender AV exclusion list and go undetected by Defender for Endpoint. We want if anybody modifies the AV scan exclusion list then MDE should trigger an alert.
Create a custom detection rule
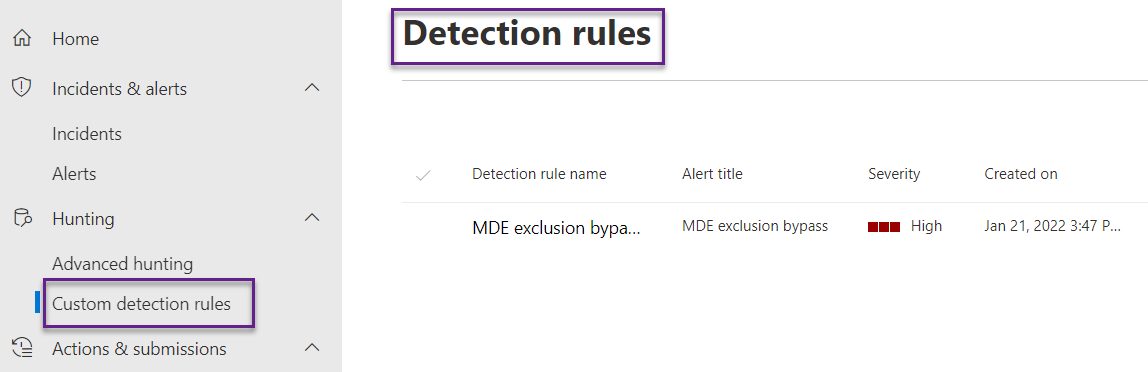
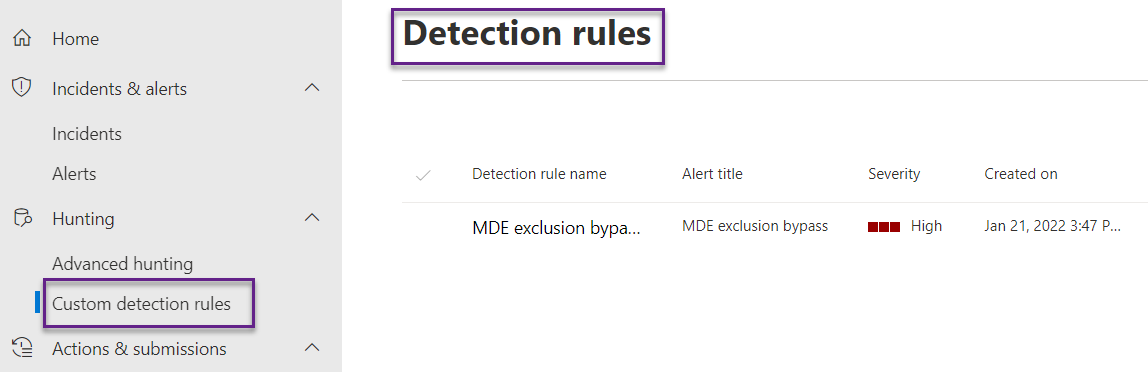
Log in to the Defender portal(security.microsoft.com) with the required permission, and navigate to Hunting->Custom detection rules. All the custom detection-created rules show here but there is no option to create the rule from here. We have to go to another place to create the rule.
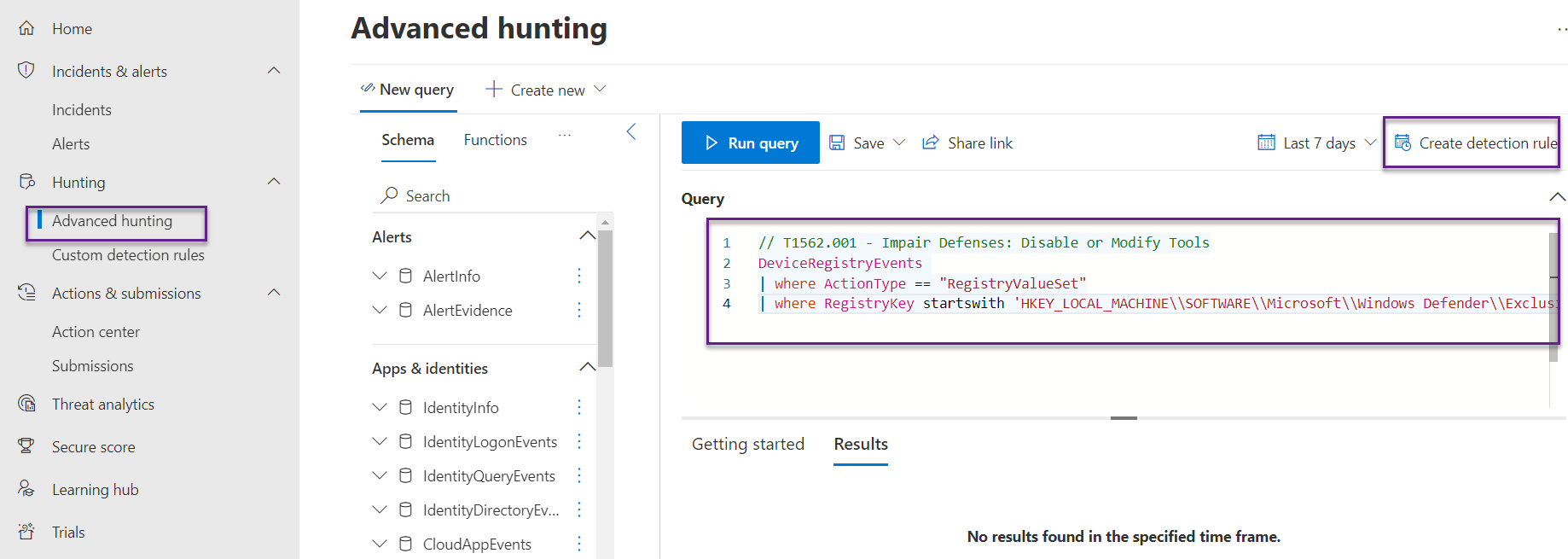
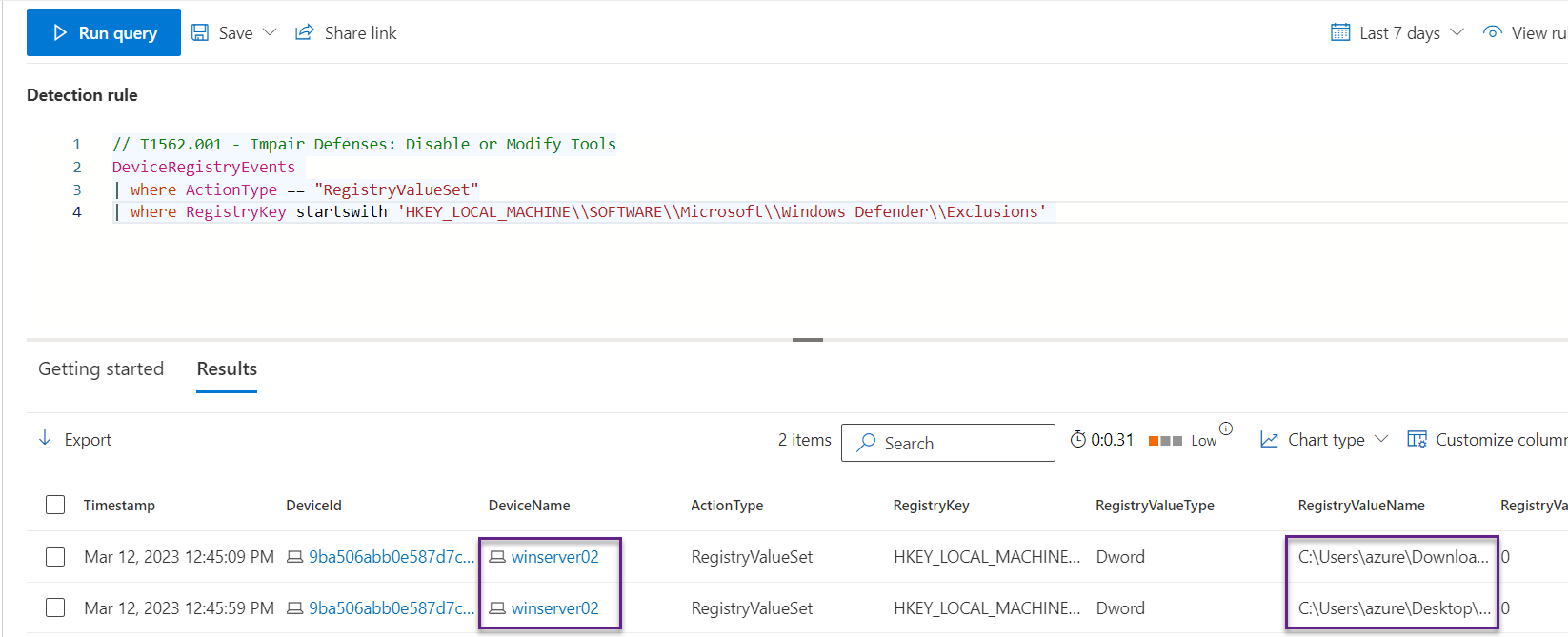
To create a custom detection rule, navigate to Hunting->Advance hunting. Paste the below query and run the query. We can see if there is any device matching this condition. Click on Create detection rule to create the rule.
DeviceRegistryEvents
| where ActionType == "RegistryValueSet"
| where RegistryKey startswith 'HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions'
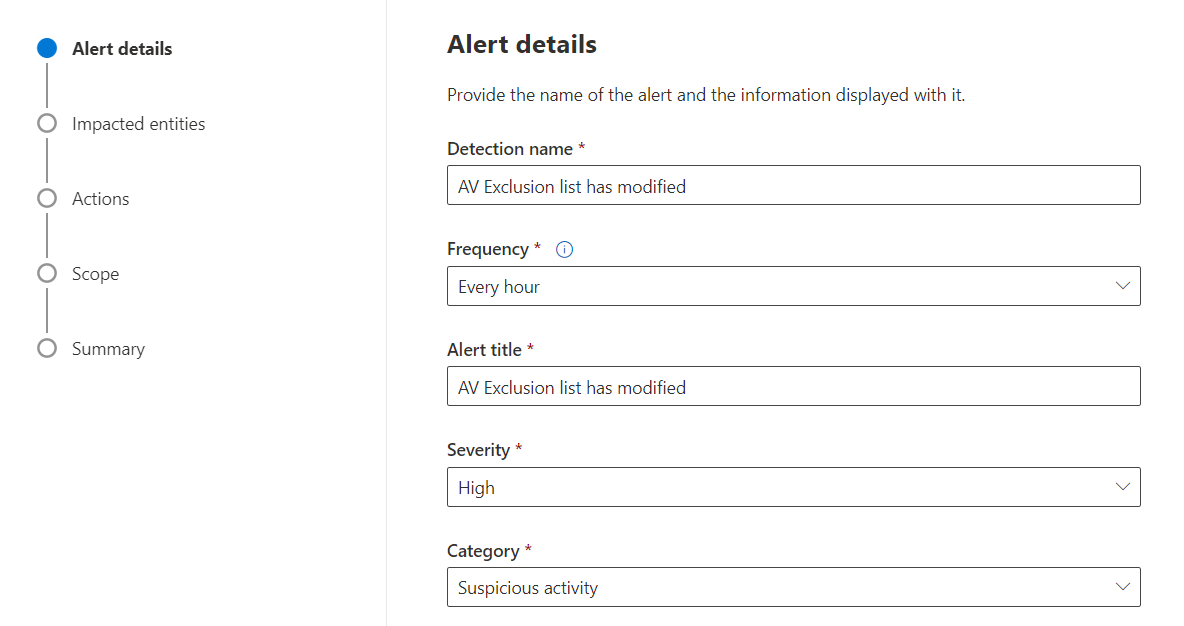
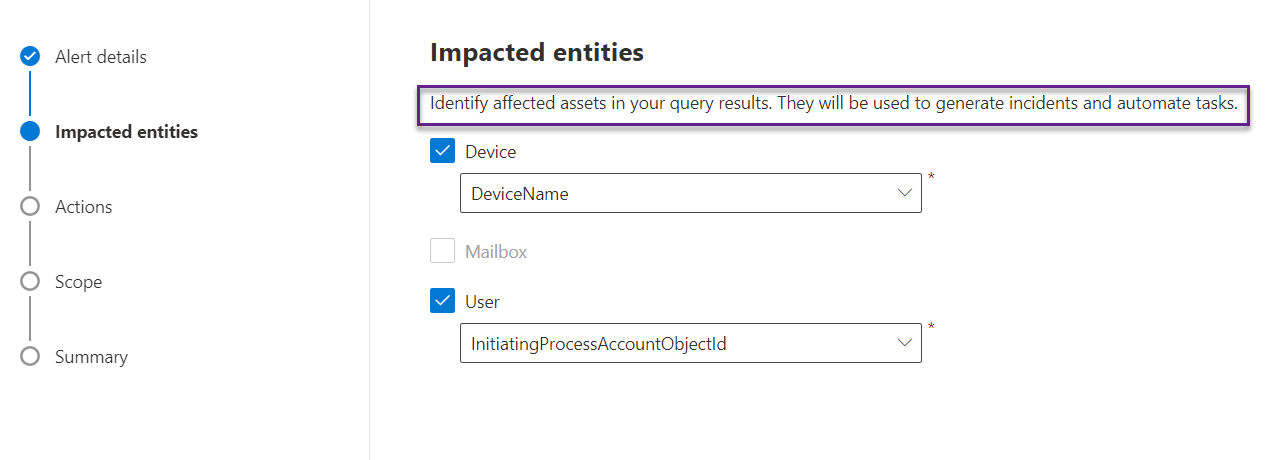
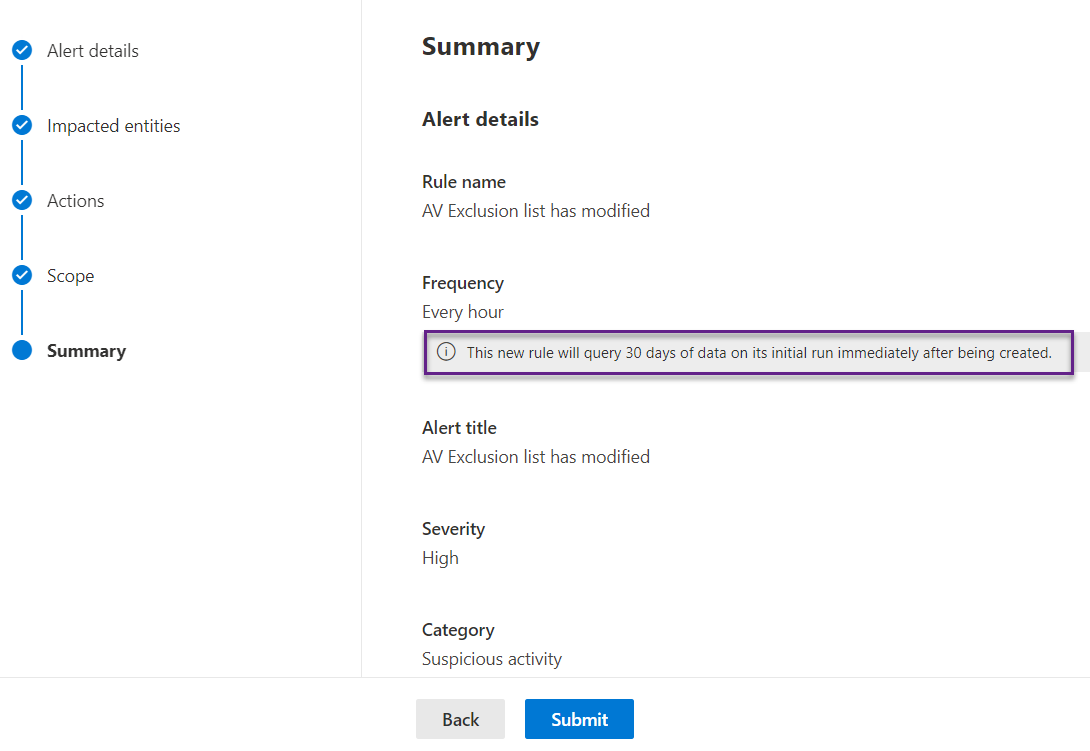
A new window opens that initiates the rule-creation process. There are several settings that need attention like frequency. We have chosen every hour. It means the rules will run every hour and generate the alert if the condition matches. We can choose from 1 hour, 3 hours, 12 hours, 24 hours, and continuous.
We also need to decide the severity of the alerts. If we have integrated with compliance and conditional policy then we need to be very careful for alert severity. If we want to treat such incidents as high risk and want to stop the user from accessing company data then we can select high.
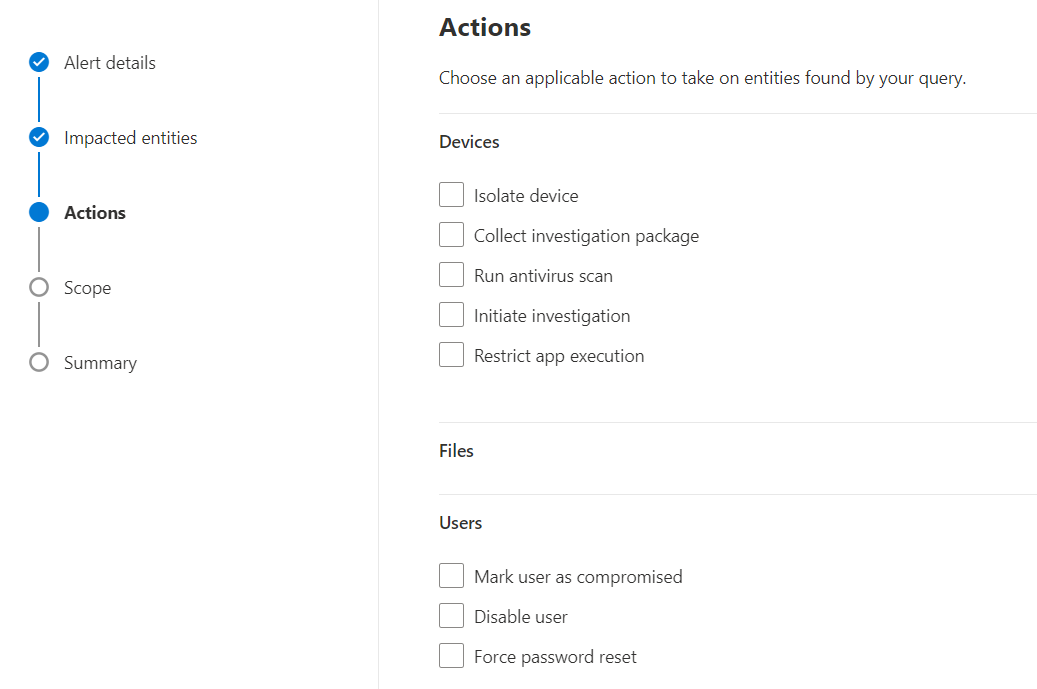
We can also take action on the device if the rule condition matches. We can isolate the device or run the AV scan or both. Below are the options we have.
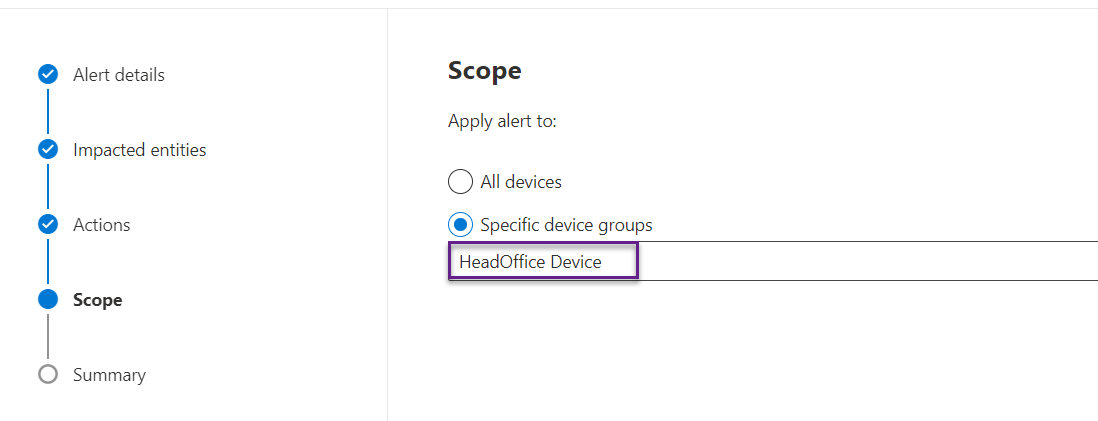
Define the scope of the rule. We have applied this policy to only the HeadOffice device group so it will be effective only for those devices.
When the rule is created then it will run for the last 30 days' data and after that as per the frequency defined. Click on Submit button and the rule will be created and will appear in the custom detection rule tab.
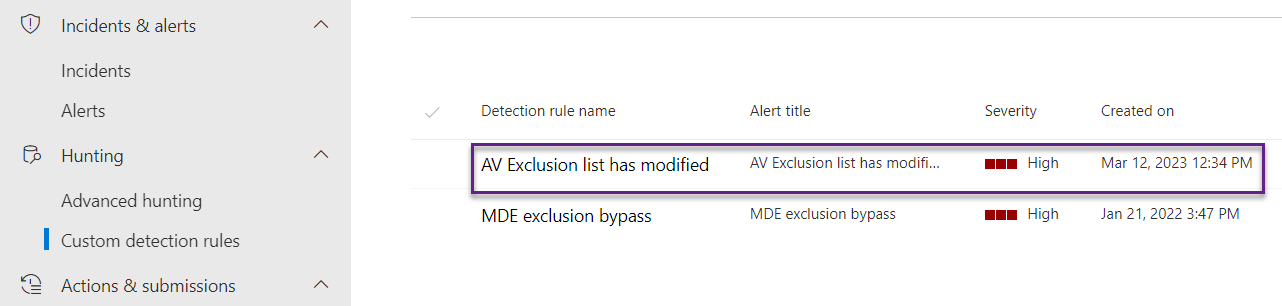
Navigate to the Custom detection rule and we can see the custom rule has appeared here. We are all done now and the rule should work as expected.
Test the rule
Now we test the rule by modifying the registry path "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions" and will see if it generates the alert or not.
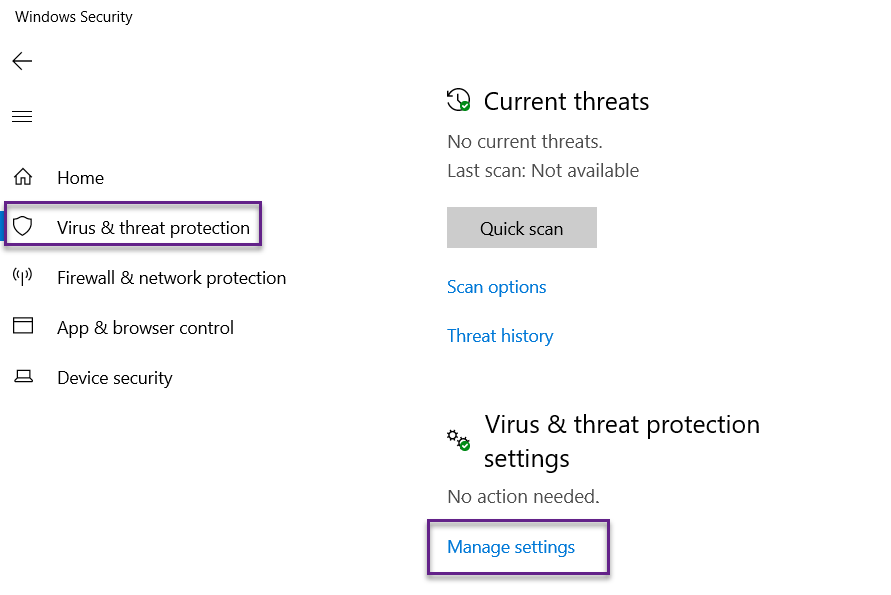
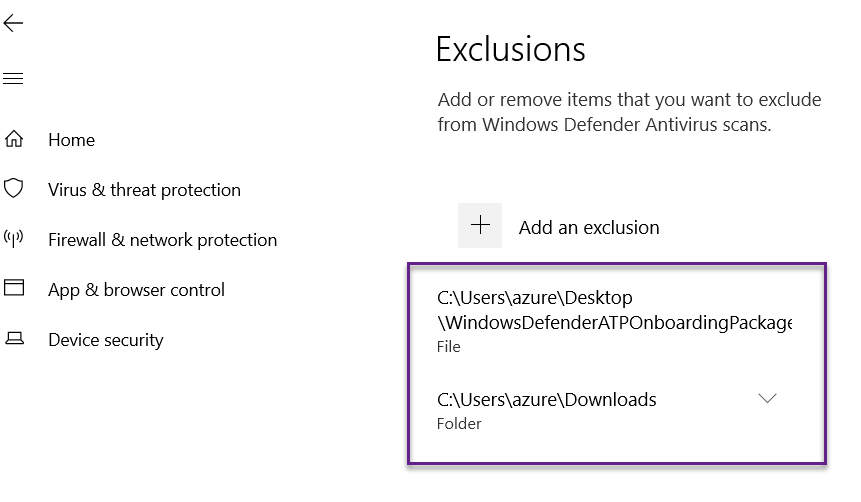
We have a server named winserver02 that has already been onboarded to Defender for Endpoint. On the server go to Windows security->Virus & threat protection->Virus & threat protection settings->Manage settings.
On Exclusions, click on Add or remove exclusions.
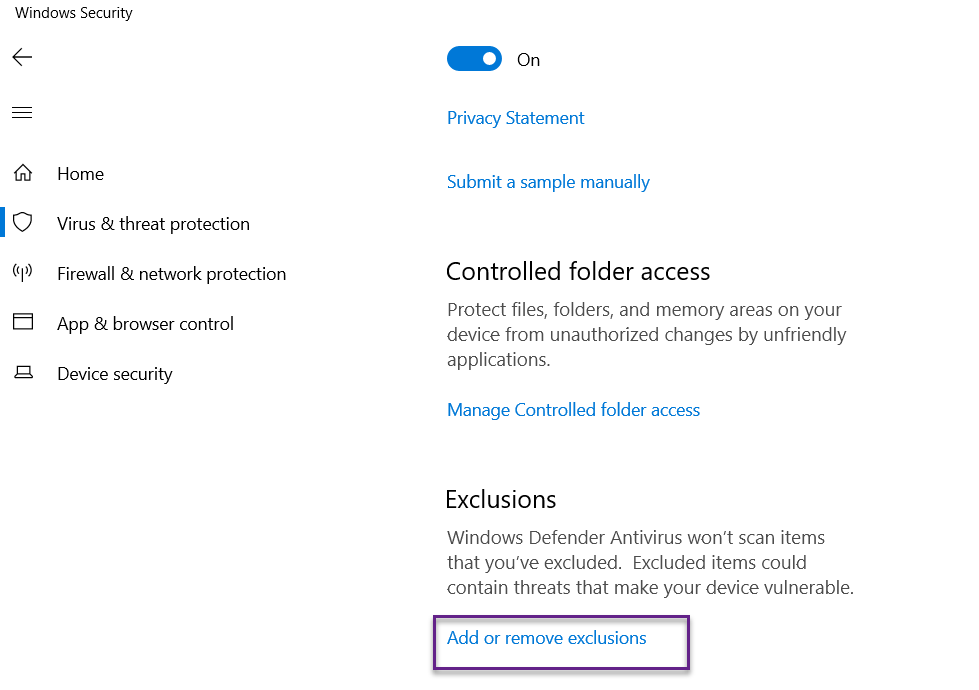
Click on Ass an exclusion and exclude certain files or folders. These changes will modify the registry value (HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Exclusions) and MDE will not scan those files or folders when the AV scan runs.
Now the changes should be detected by MDE's custom rule and should generate an alert. As we have defined the rule every hour so we have to wait for an hour or we can go and run the rule manually as below.
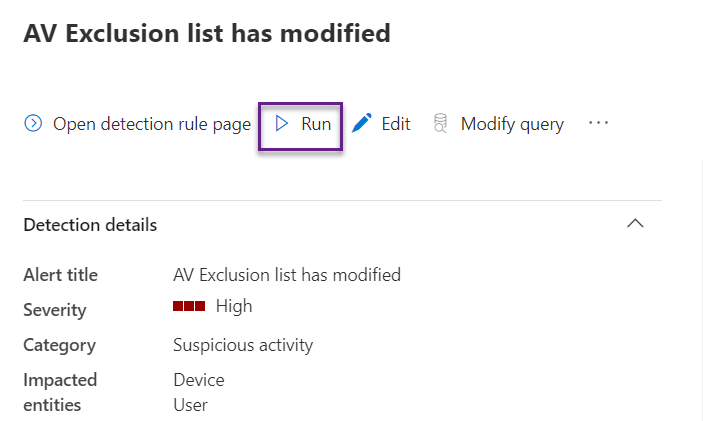
If we run the same query then we can see the MDE has detected those changes.
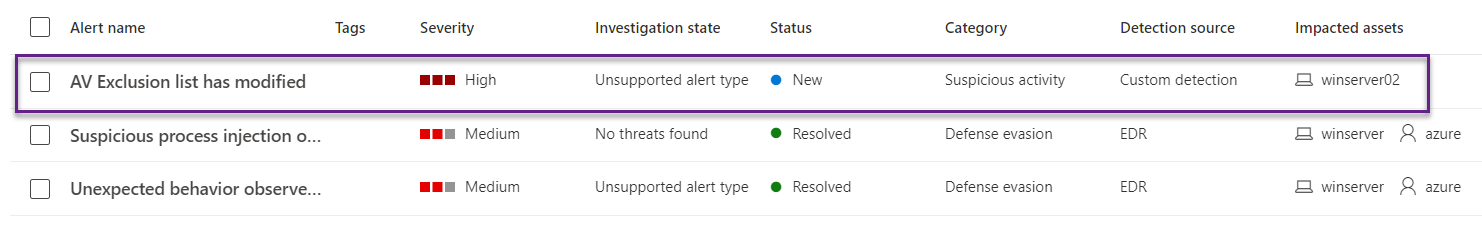
Now the alert has been generated and displayed on the portal and the rule is working as expected.
We can use any query to create the custom detection rule.
Hope this was helpful, contact me on Twitter @sakaldeep for any queries.