15.0 Defender for Endpoint(MDE): Endpoint Security policy
The device onboarded to Defender for Endpoint (MDE) needs a security policy applied to manage Defender security settings. Once the device receives the policy, the Defender for Endpoint components on the device enforces the policy and reports the device's status. There are many ways to apply policy:
- Using Intune if the device has registered to Intune.
- Using Configuration Manager if the device is being managed by SCCM.
- Using Group Policy if the device is domain joined.
- From the MDE portal (Endpoint Security Policies) if your device does not fall in any of the above.
Earlier it was not possible to assign security policy from the MDE portal (security.microsoft.com), we had to rely on either Intune, Configuration Manager, and Group Policy. To achieve this, the device must be managed by those tools that might required to be domian joined. If the device is not domain-joined and managed by those tools then it is very difficult to apply any security policy.
There was a requirement from a customer on how to apply policy for such devices that have only been onboarded to MDE and Microsoft addressed it finally. It is made possible by registering MDE onboarded devices to Entra ID using synthetic registration. Below is from the Microsoft official docs.
Security settings management uses a synthetic registration for devices that don’t fully register in Microsoft Entra ID, and drops the Microsoft Entra hybrid join prerequisite. With this change, Windows devices that previously had enrollment errors will begin onboarding to Defender and then receive and process the security settings management policies.
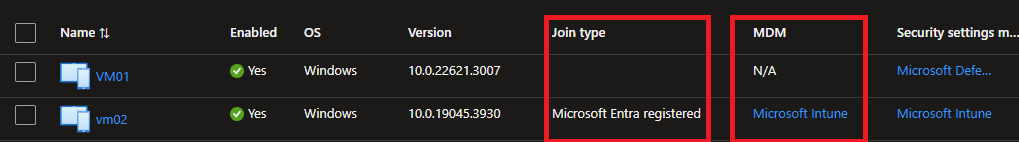
To filter for devices that were unable to enroll due to failing to meet the Microsoft Entra hybrid join prerequisite, navigate to the Devices list in the Microsoft Defender portal, and filter by enrollment status. Because these devices are not fully registered, their device attributes show MDM = Intune and Join Type = Blank. These devices will now enroll with security settings management using the synthetic registration.
After enrolling these devices appear in the device lists for Microsoft Defender, Microsoft Intune, and Microsoft Entra portals. While the devices won’t be fully registered with Microsoft Entra, their synthetic registration counts as one device object.
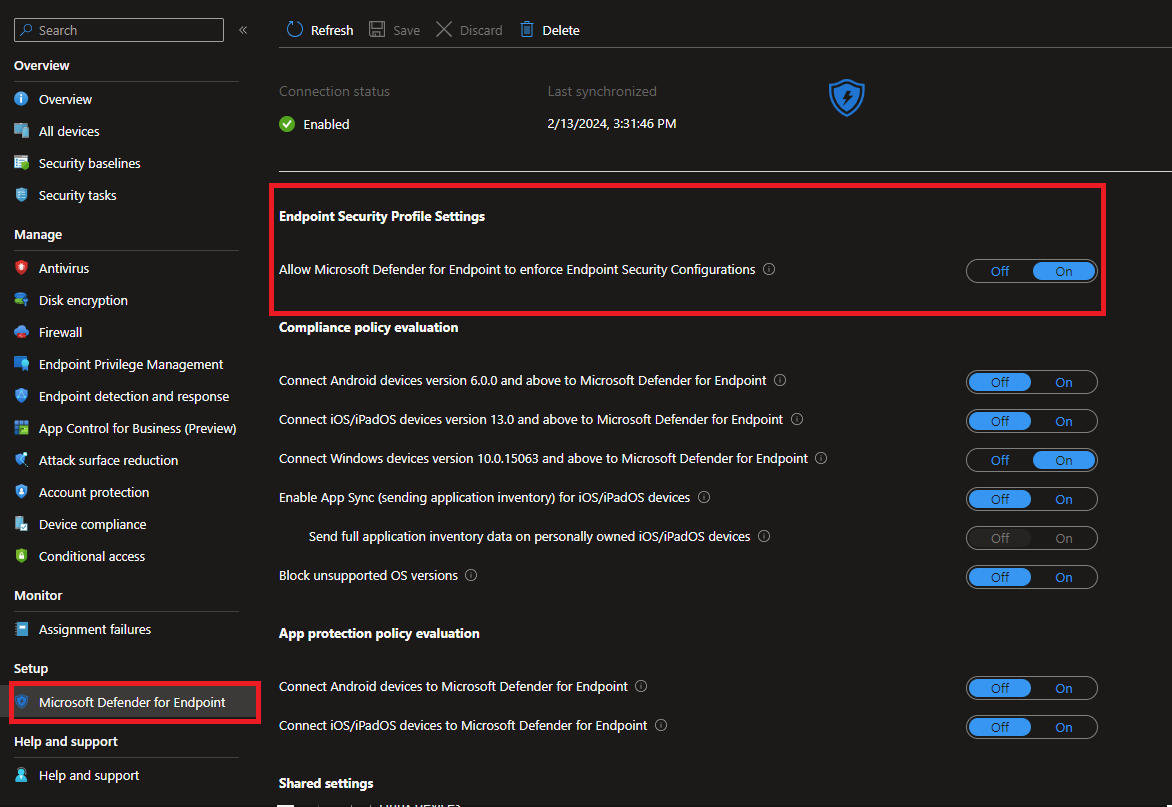
Some settings need to be turned on in both Defender and Intune portals to get the device enrolled to Entra ID.
The below settings need to be turned on in the Intune portal. Intune.microsoft.com->Endpoint security->Microsoft Defender for Endpoint.
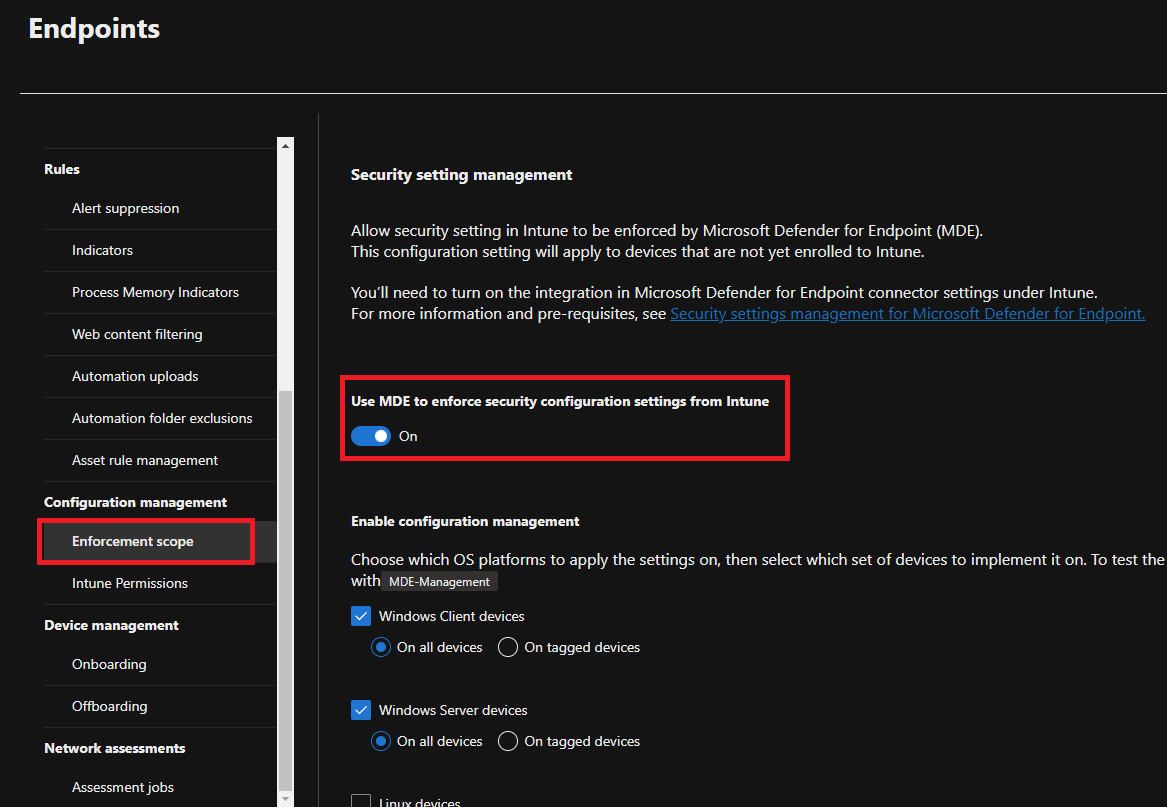
The below settings need to be tuned on the Defender portal. Security.microsoft.com->Settings->Endpoints->Enforcement scope.
Once the device is onboarded with the Entra ID then it looks like the below on the Entra ID portal.
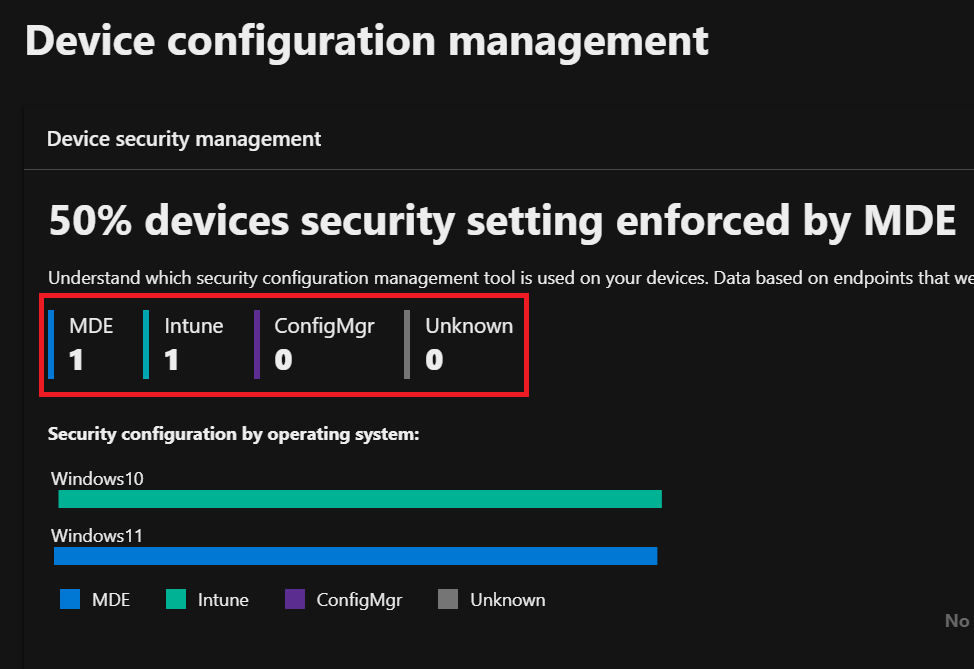
On the Defender portal, we can see the device vm01 is managed by MDE.
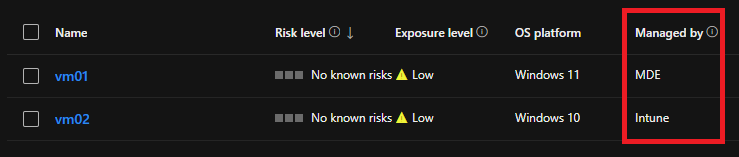
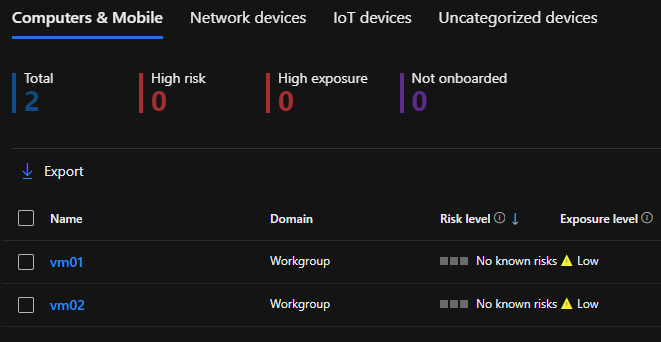
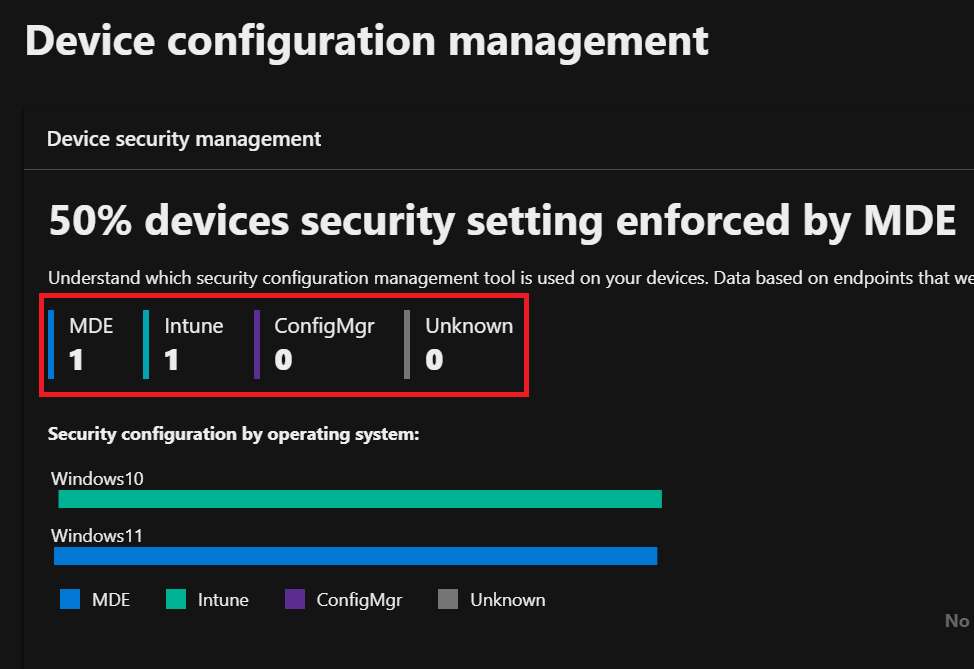
We have two devices named VM01 and VM02. VM02 is registered and managed by Intune and VM01 is managed by MDE.
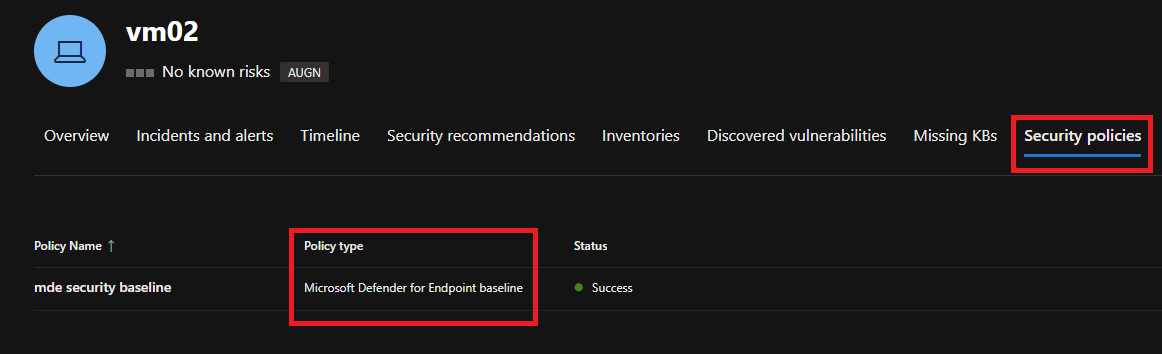
As VM02 is being managed by Intune we have applied a security policy from Intune. We can see the policy type is 'Microsoft Defender for Endpoint Baseline'.
For VM01, there is no policy has applied.
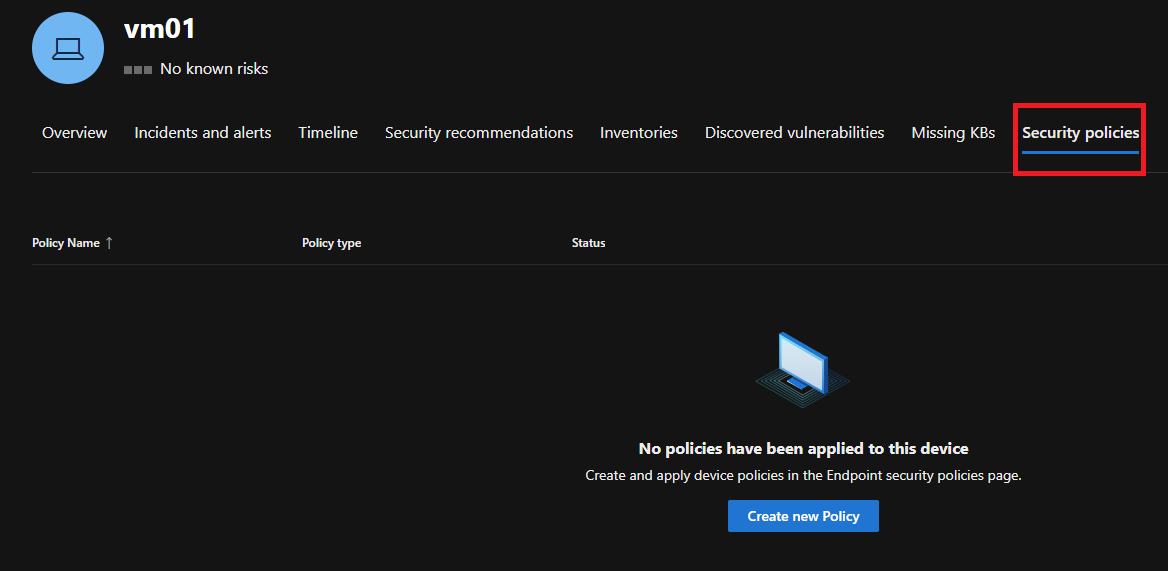
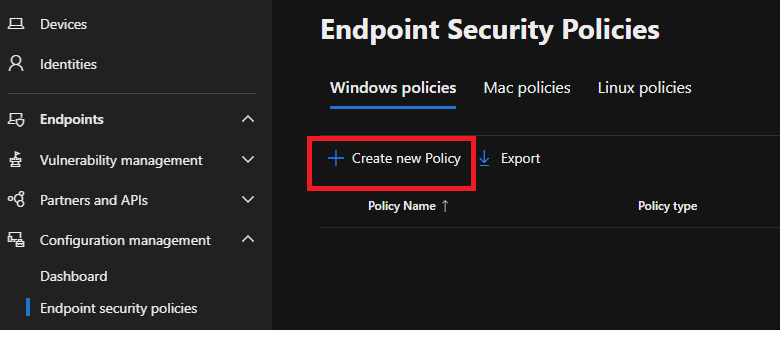
Let's apply the security policy to VM01 from the Defender portal. Go to, Endpoints->COnfiguration management->Endpoint security policies.
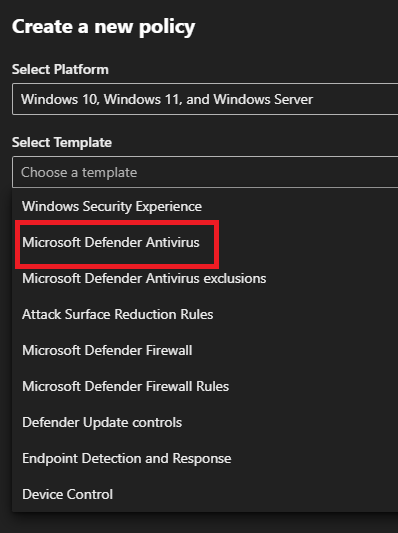
There are many types of policies, we choose here 'Microsoft Defender Antivirus' policy.
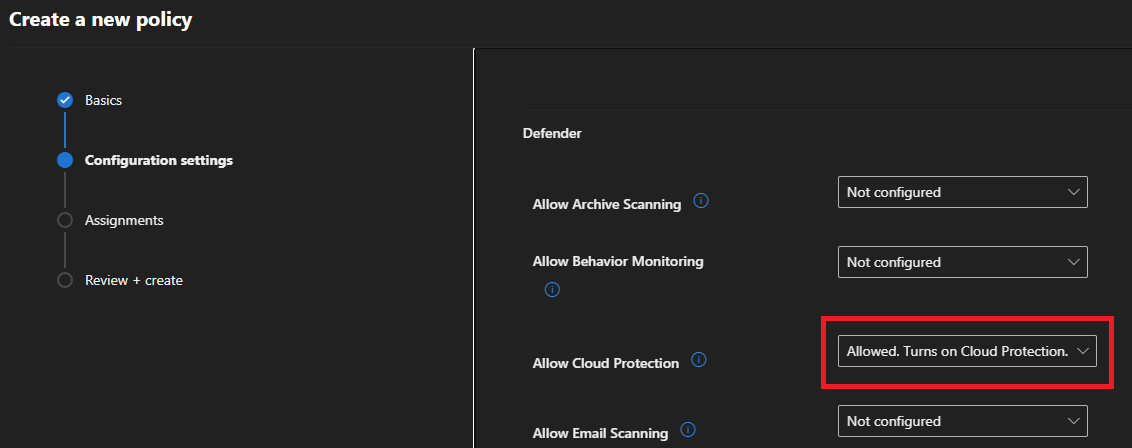
Select all the Antivirus settings as per your organization's needs.
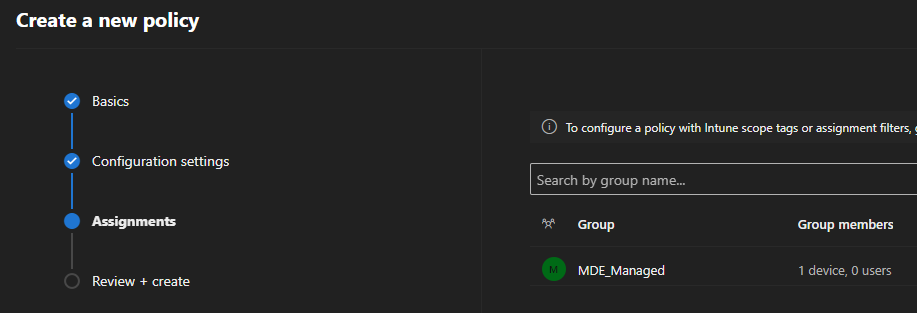
Assign the policy to the group. In this case, Vm01 is a member of the group called 'MDE_Managed'.
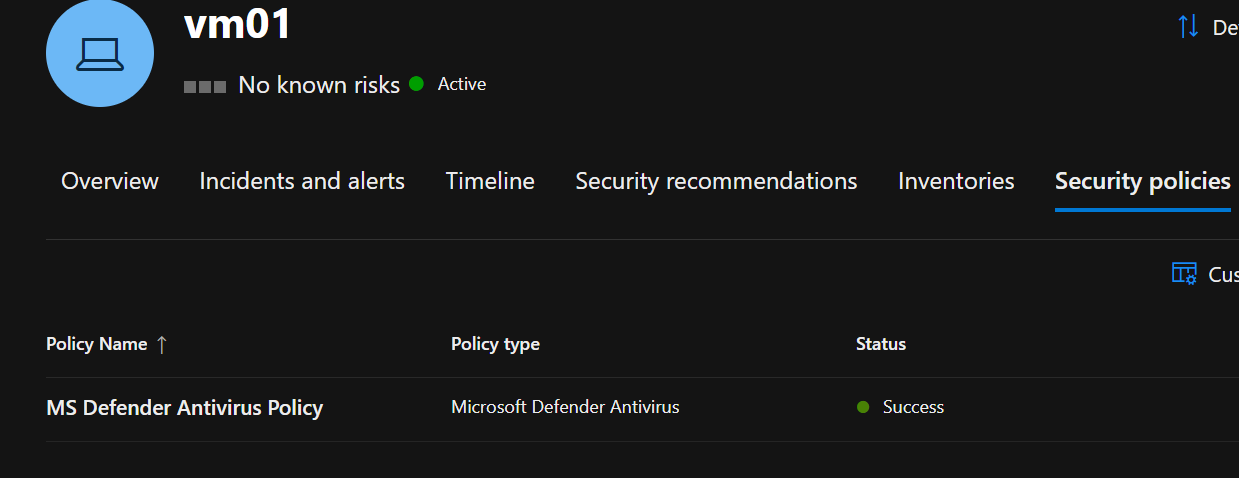
We can see below the policy type is 'Microsoft Defender Antivirus' that has been assigned from the Defender portal.
We can also see the summary of security policies, one policy has been assigned from MDE and another from Intune.
Hope this was helpful, contact me on Twitter @sakaldeep for any queries.