9.0 Defender for Endpoint(MDE): Device Group & Roles
In Defender for Endpoint, the device group is a collection of devices. The device group can be created based on certain criteria or characteristics like operating system, location, device type, user group, and tag. In this post, we create based the device group based on the tag.
A device group is very useful for management purposes like applying a security policy to a certain group of devices.
Login MDE portal (security.microsoft.com), Settings->Endpoints->Device groups. In the image below, we can see there is a default device group. This device group is created automatically and the devices belong to this group. So when we apply any policies, it will pick the default group and will be applied to all the devices.
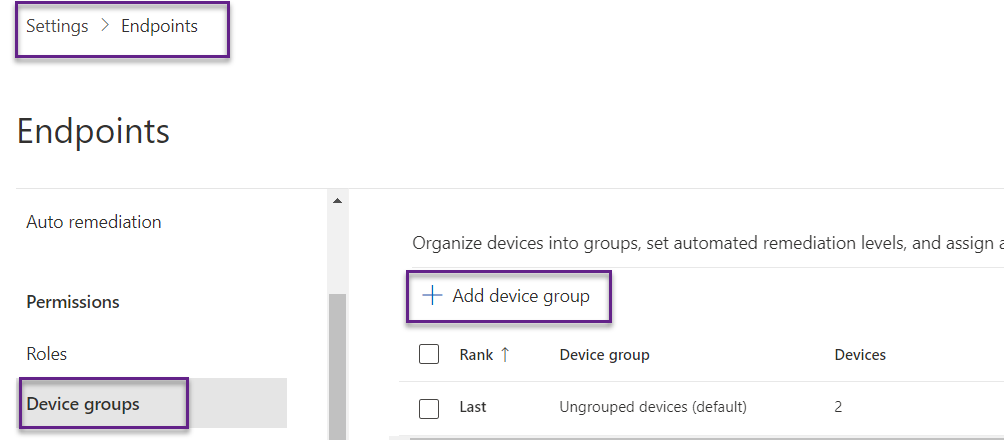
Here, we create a device group for the head office based on the tag. We have created a head office tag in this post - 8.0 Defender for Endpoint(MDE): Device Tag. After that, we can a certain policy to head office devices.
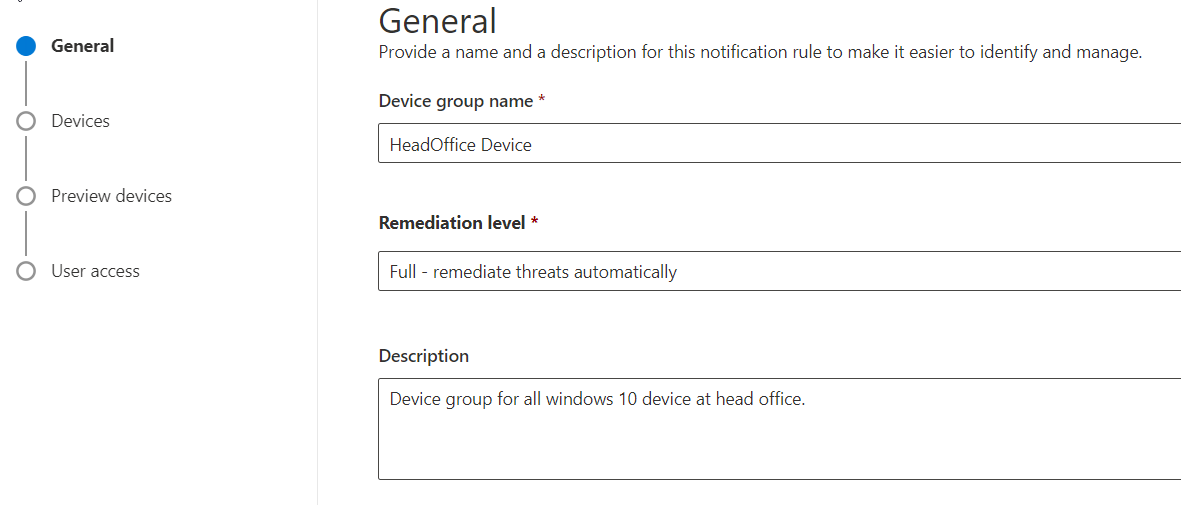
Give meaningful names and descriptions. Choose a full remediation level. Full mediation means MDE will start the investigation and remediate it automatically when threats are found.
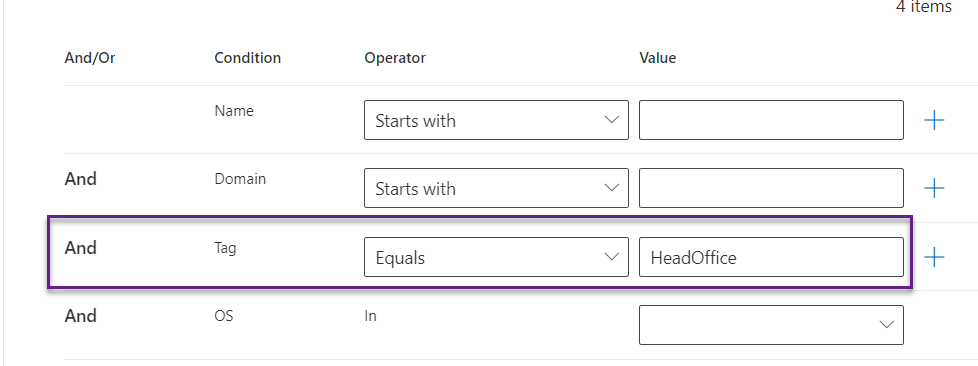
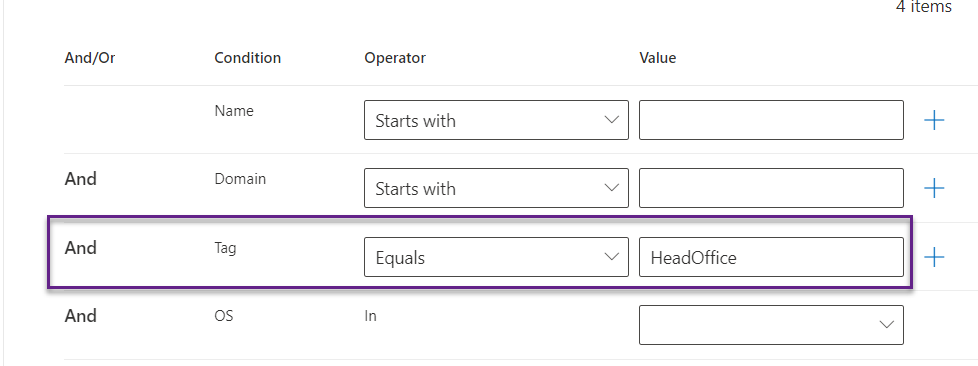
We can see there are multiple criteria, here we have chosen the tag. This will create the device group for all the devices having the tag HeadOffice.
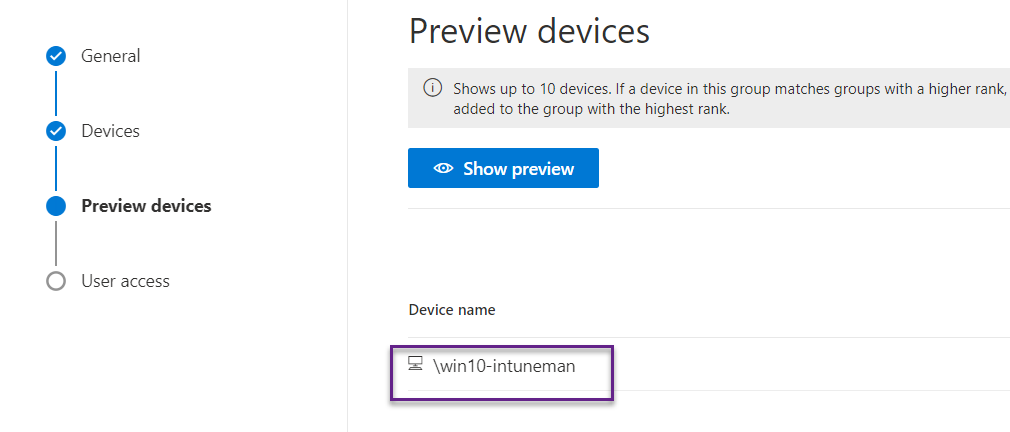
We can also check is there any devices is based on the supplied criteria. Here, we can see there is a device having that tag.
We can also define user access for the device group. This means who can access those devices. Suppose we want only the head office admin can manage the head office device then we can define it here. We have not created any roles yet so here let's give access to everyone.
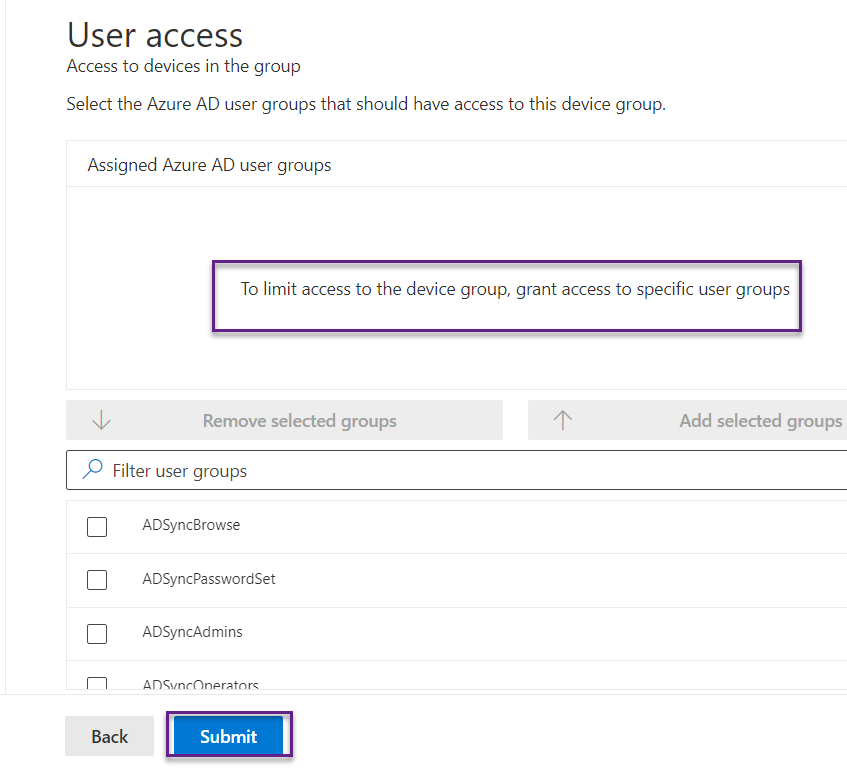
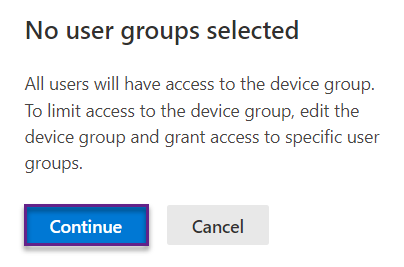
When we click on Submit button then we get the below message that no specific user group has been defined so all users can access it.
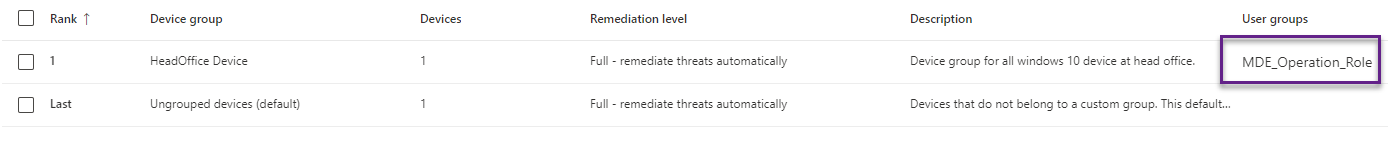
The device group has been created that has 1 device.
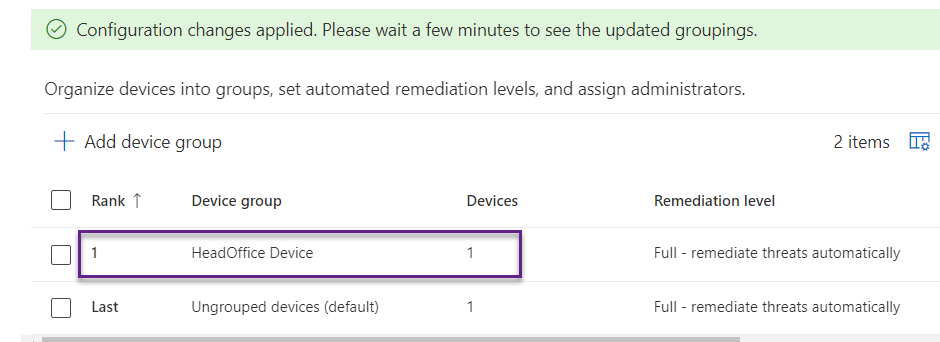
Rank: The device group with a lower rank has higher priority. This group has ranked 1 so this device has the highest priority. It means if the device meets the criteria to become a member of this group and another group then it will become a member of this group.
Device: Devices show the number of devices in this group.
Remediation Level: This shows that is the remediation level for all those devices.
In the below image, we are blocking certain IP addresses and we can get the option to select the scope of it. We can choose the device group we created.
MDE Roles
Defender for Endpoint has several roles like security operator, security admin, reader, threat and vulnerability management administrator, and threat and vulnerability management user.
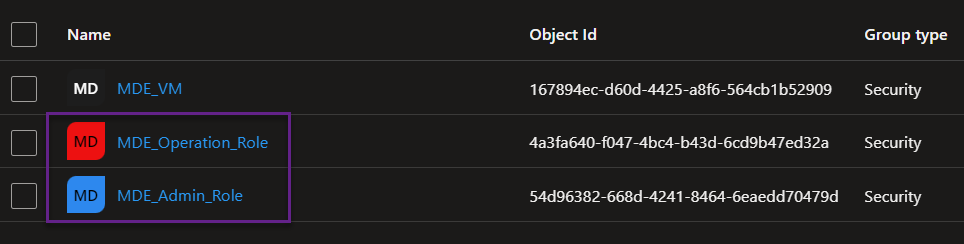
We need an AAD group to create roles in MDE. In the below image, we have created two AAD groups MDE_Operation_Role and MDE_Admin_Role. We will use these groups for creating roles in MDE.
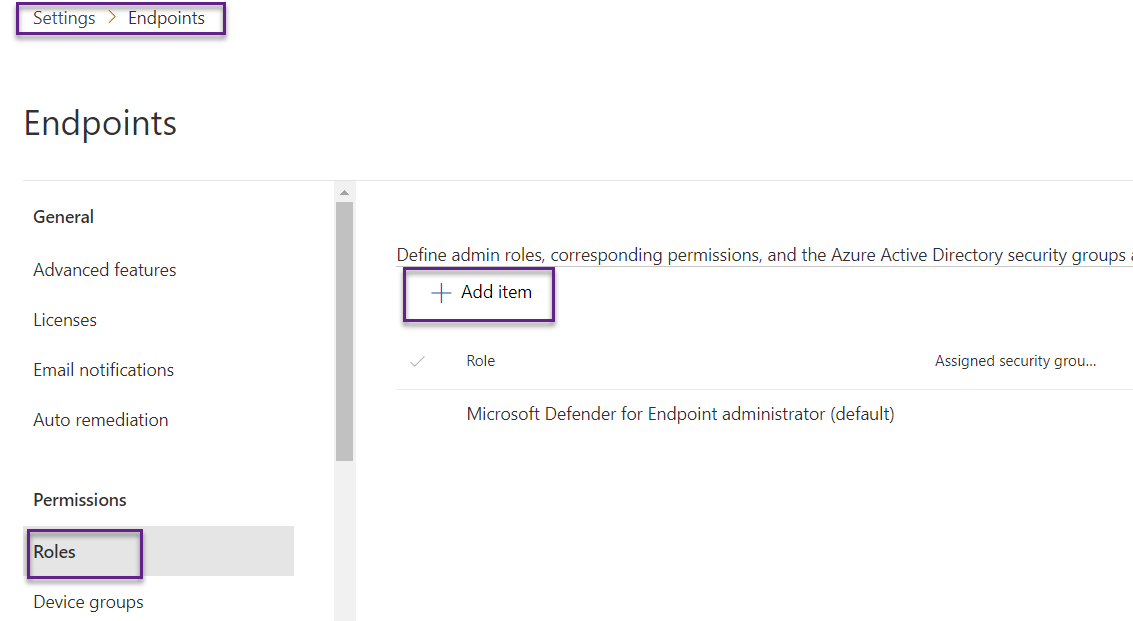
Login MDE portal (security.microsoft.com), Settings->Endpoints->Roles->Add Item.
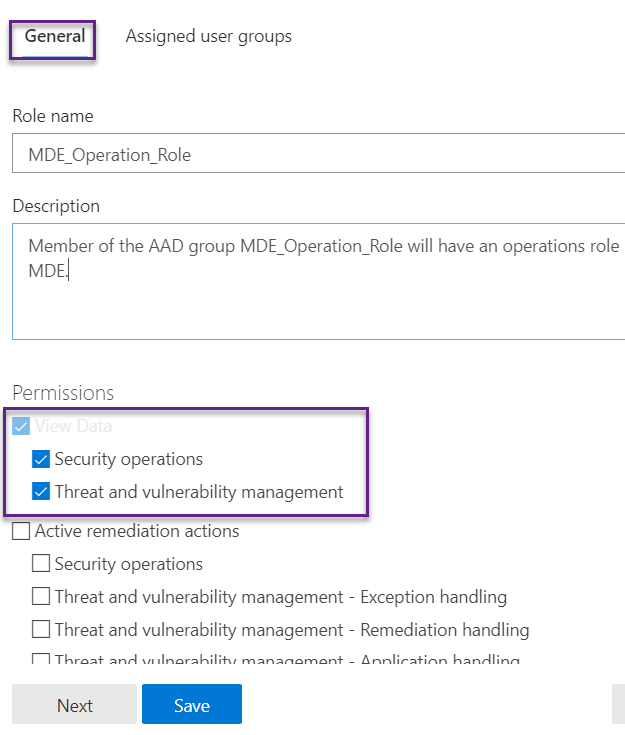
Provide meaningful names and descriptions. Choose the permission that you want from the list below.
Assign the user group, here we have to choose the AAD group name. Search for the group that we want and click on Add selected groups.
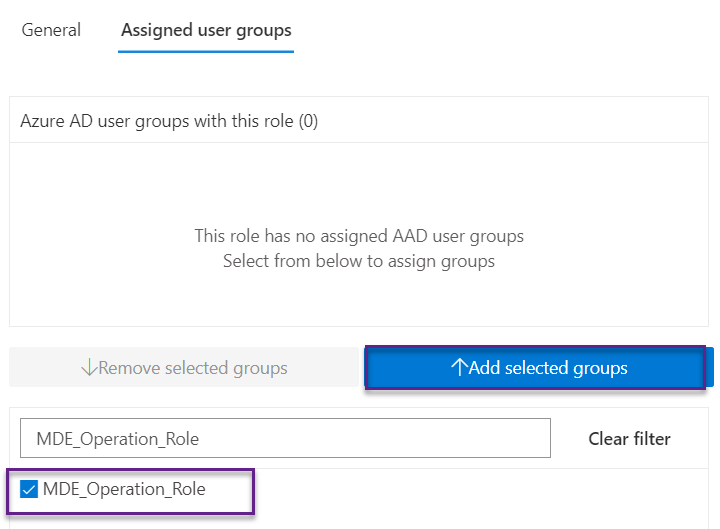
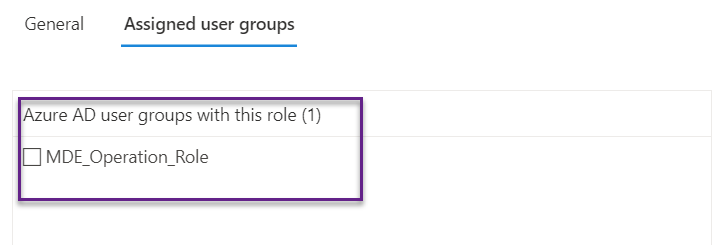
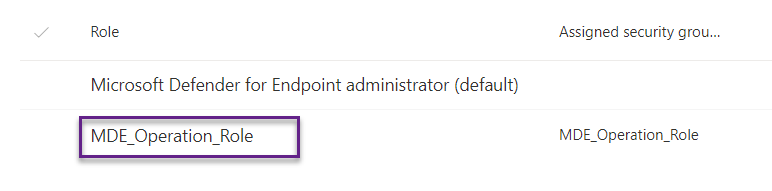
The role has been created as below image. It means all the members of the AAD group MDE_Operation_Role have Security operations and Threat & Vulnerability management permission.
Combine Device Group and Roles
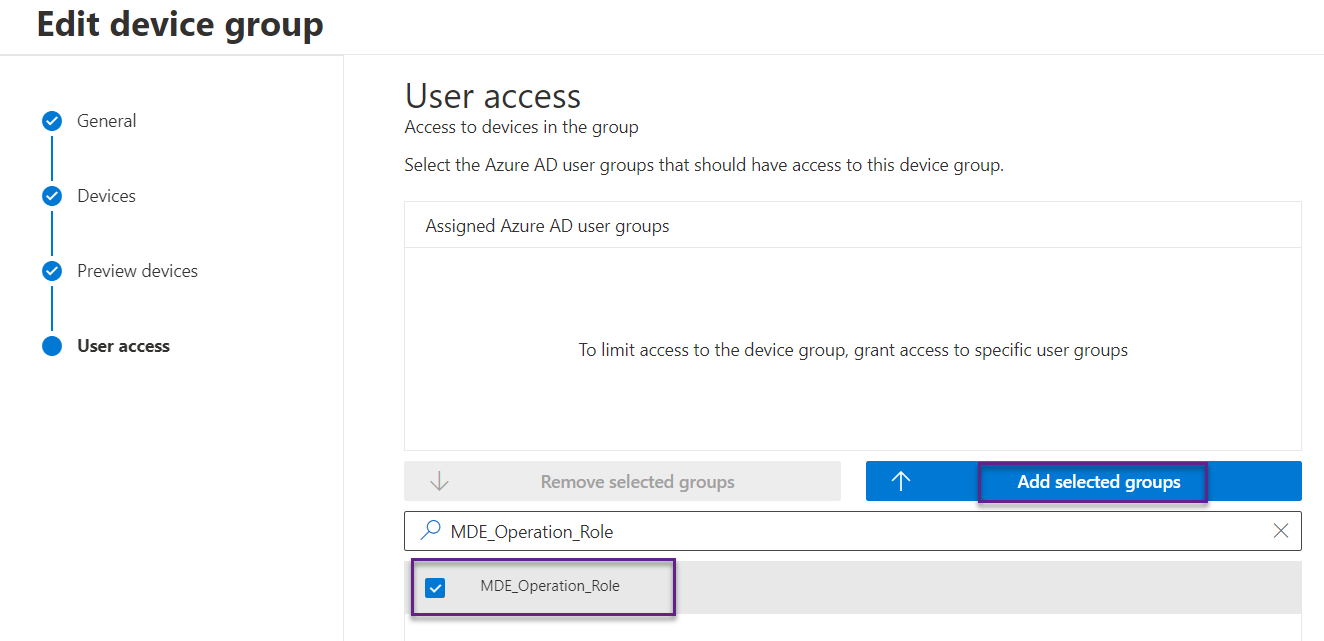
Now we have both device groups and roles created then we can combine them. Suppose we want devices in head office group and be only accessible by MDE_Operation_Role members.
Navigate the device group that we created and ho the user access window, search for the group, and add it.
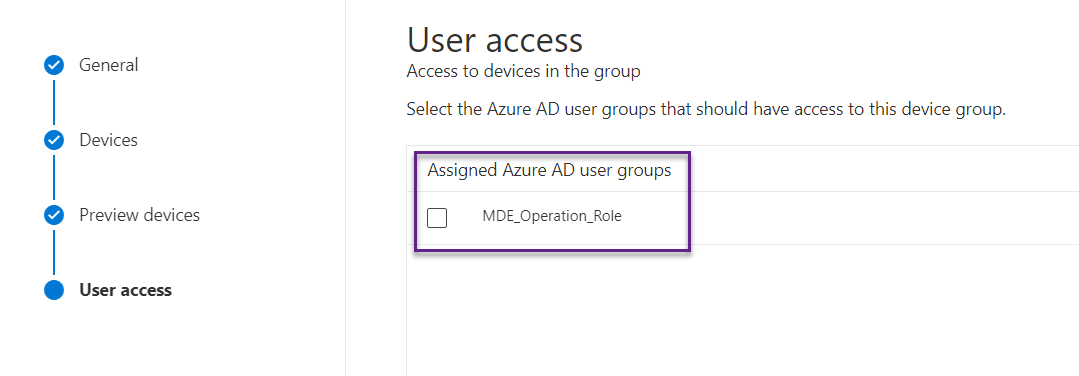
If we scroll left on the device group page, we can see the device group HeadOffice Devices has user group MDE_Operation_Role.
Conclusion
Device groups and roles are very powerful tools in Defender for Endpoint to manage the security of the devices that improve visibility and control in the organization.
Hope this was helpful, contact me on Twitter @sakaldeep for any queries.