Can Application Change Analysis do the same role of FIM for Azure App Service?
In this post, we will discuss, can Application Change Analysis do the same role of FIM for Azure App Service?
Background of this requirement
We are using Azure VM to host our LOB applications. To comply with PCI DSS requirement 11.5 - File Integrity Monitoring (FIM), We use Defender for Cloud's FIM (more details here) and we are good. Now we have decided to move from Azure VM to Azure App service to get the advantage of PaaS like no patch management, auto-scale, etc. Once We move from VM to App Service, we are looking for a solution that acts as an FIM solution for App service so can comply with PCI DSS requirement 11.5 as Defender for Cloud's FIM is only supported for VM (not for App Service). Why Defender for Cloud's FIM does not support App Service - Azure App service runs in a sandbox and it has its own restriction for the registry, file system, etc. as described in Github docs.
Below is the official PCI DSS #Requirement 11.5 that the auditor is looking for to comply with the App service.
"Deploy a change-detection mechanism (for example, file-integrity monitoring tools) to alert personnel to unauthorized modification (including changes, additions, and deletions) of critical system files, configuration files, or content files; and configure the software to perform critical file comparisons at least weekly."
Azure App Service is a hardened platform, with most of the underlying VMs are not accessible so there isn’t a need to do things like monitoring for file changes to the OS files, monitoring for changes to the Windows registry, etc. Such type of access is blocked by the App Service platform. However, if anyone is considering the changes in files/code of the App Service then we will see if the above requirements can be achieved using Application Change Analysis for App Service.
What is Application Change Analysis
Application change analysis is a change tracking solution for the Azure infrastructure and application level that applies to the virtual machine, App service, function, networking, data, etc but in this post, we only talk about App service deployment changes (files and code).
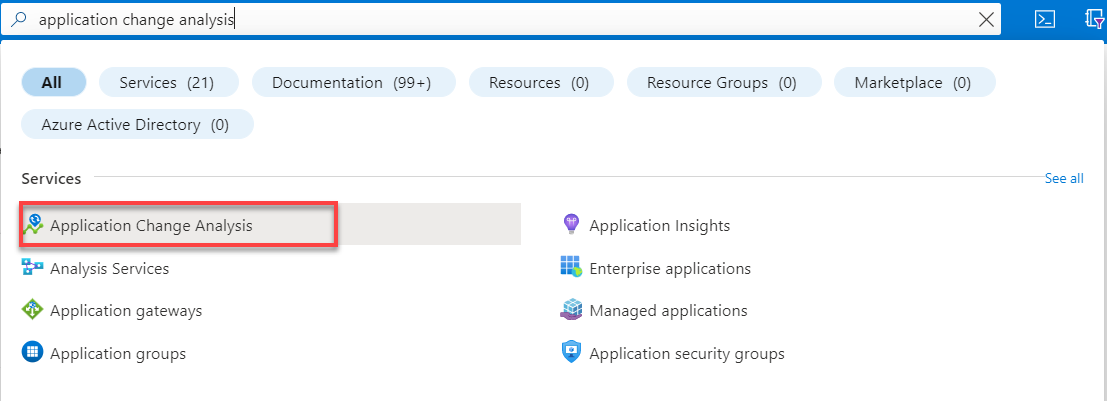
Go to Azure portal->Search application change analysis.
Click on Configure.
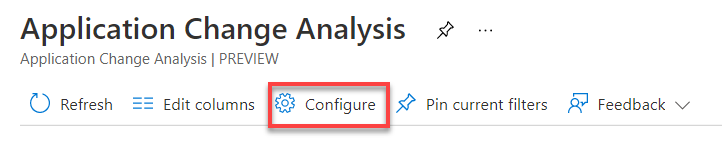
Select the App Service plan or specific App service to enable Application change analysis.
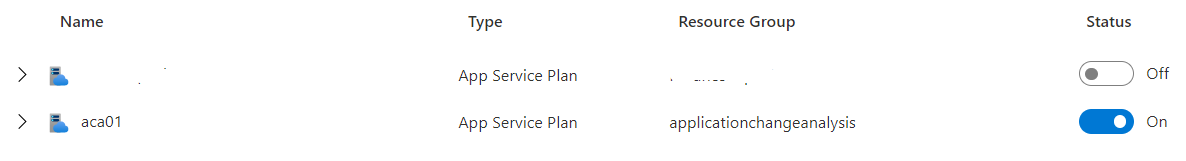
Note: once Application Change Analysis is enabled for the App service, the App Service must be restarted.
Limitation: Currently, all text-based files under site root wwwroot with the following extensions are supported.
*.json
*.xml
*.ini
*.yml
*.config
*.properties
*.html
*.cshtml
*.js
requirements.txt
Gemfile
Gemfile.lock
config.gemspecTo test if it working for the App service, we are adding a few test files in wwwroot using the App service editor as below.
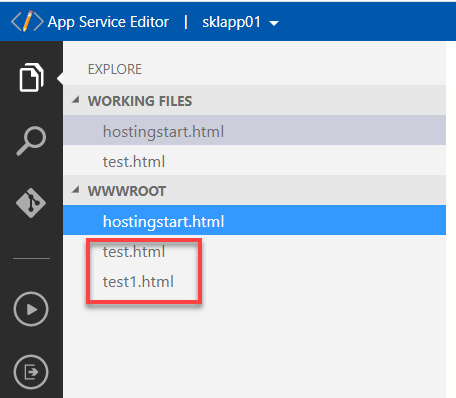
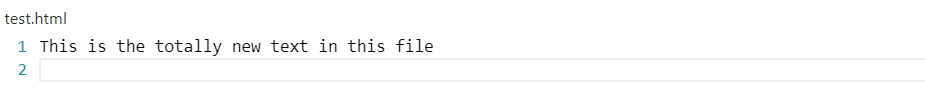
We also added content to the test.html file as below.
Application Change Analysis dashboard is showing all the changes as the file has been added and the content inside it.
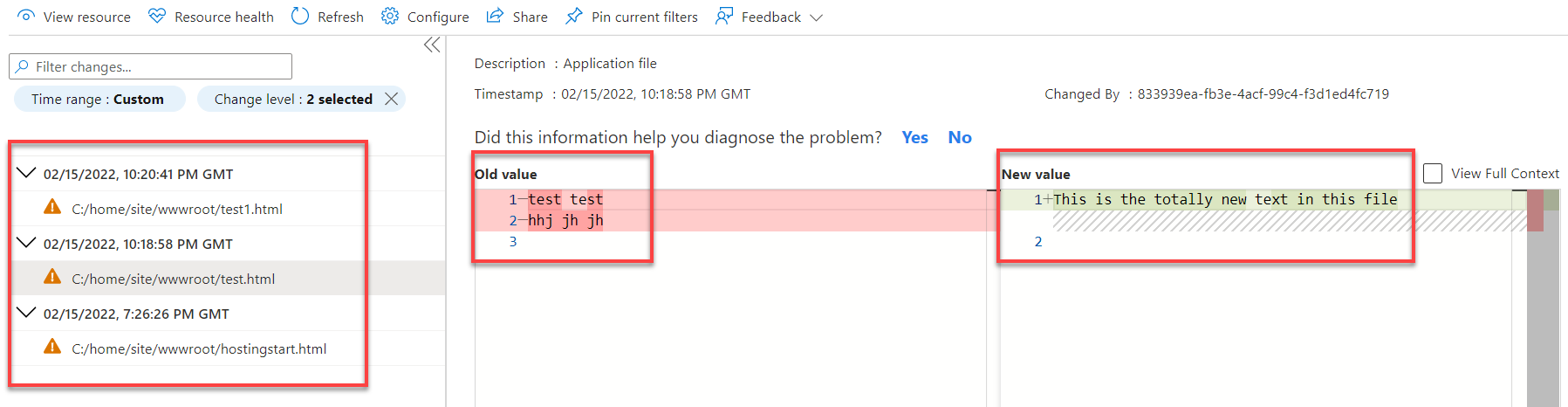
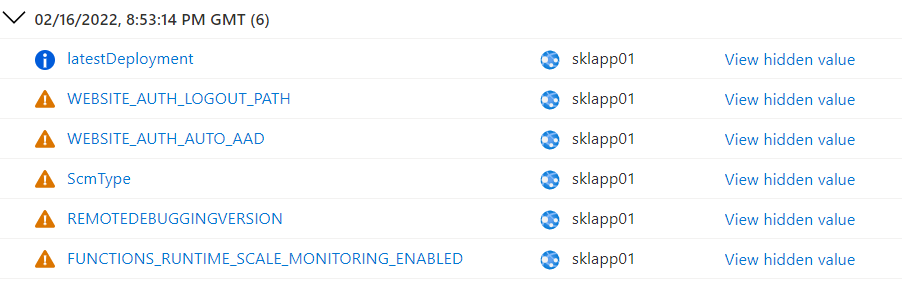
Now we are pushing code using Azure DevOps CI/CD pipelines and will see if all the changes are being tracked and detected by Application Change Analysis. Below are the resource level changes tracked for the App service.
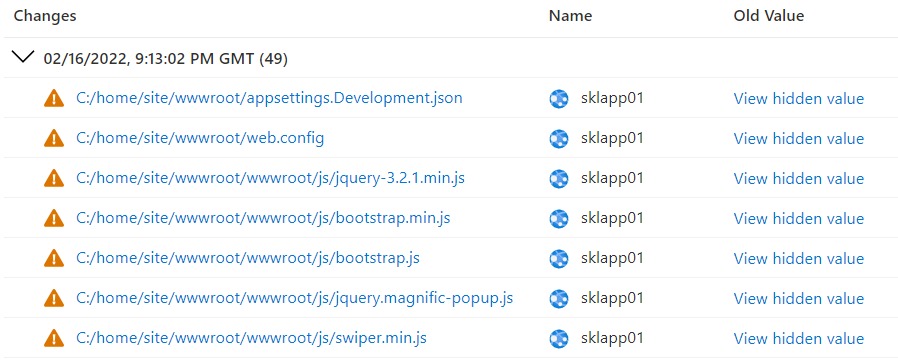
This is the code level changes tracked. We can see many more files are added to the source code and it's being detected by Application change analysis.
Alert
One of the FIM requirements is to trigger the alert when change is detected. Application Change Analysis will dump all the changes into the Log Analytics and we can configure the alert there. Its currently in private preview as per the Github docs - Enable Change Notifications Private Preview - Application Change Analysis
Cost
Application Change Analysis is a free service.
Conclusion
Application Change Analysis is detecting all the changes at the resource level as well as code level for App service and also triggers an alert in the case of change detected. It seems it fulfills all the requirements and does not see why it can't act as an FIM solution for the App service.
Hope this was helpful, contact me on Twitter @sakaldeep for any queries.