Microsoft Copilot for Security: Elevating Microsoft Security Technology

In the ever-evolving landscape of cybersecurity, staying ahead of threats is a constant challenge for organizations worldwide. Microsoft Copilot for Security emerges as a beacon of innovation, leveraging the power of Generative AI to revolutionize how security teams operate.
Microsoft Copilot for Security (aka Microsoft Security Copilot) is not a replacement for current Microsoft security technology. It complements existing Microsoft security technologies such as Microsoft Defender XDR, Microsoft Sentinel, Microsoft Intune, or Microsoft Defender Threat Intelligence. It is designed to enhance the overall security experience and contribute to upskilling efforts rather than serving as a replacement. It augments human expertise maintaining a human-centric approach to decision-making.
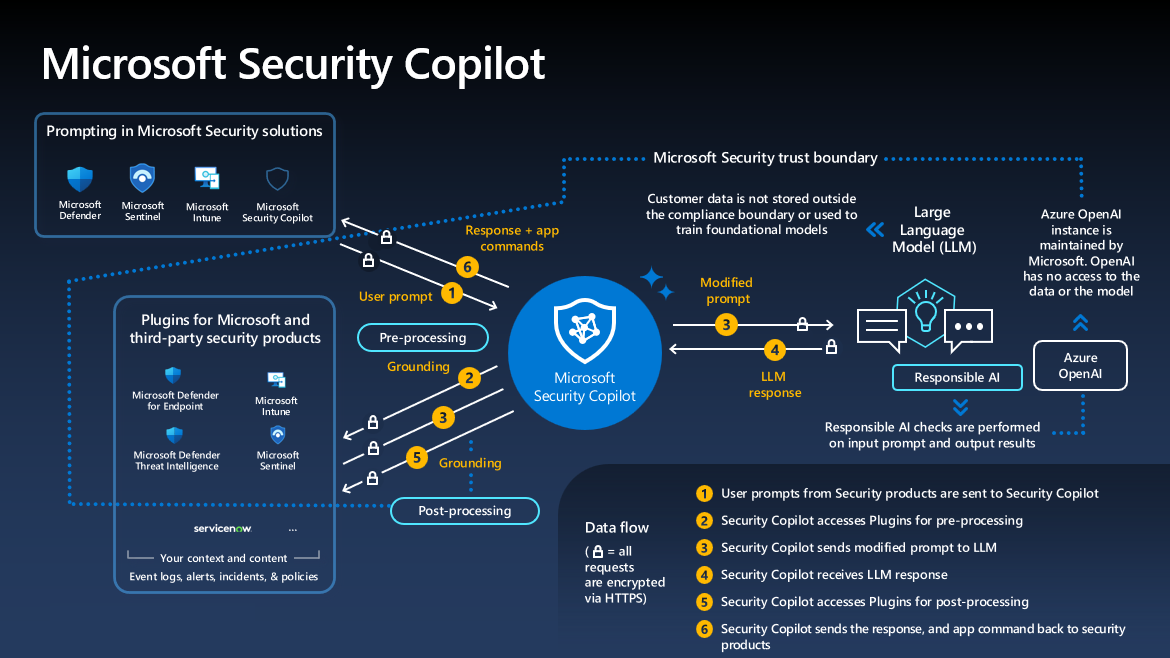
Microsoft Copilot for Security leverages the power of OpenAI's GPT-4 along with Microsoft's security-specific model. It’s a paradigm shift in cybersecurity defense. By integrating with Microsoft’s suite of security solutions, it provides an intuitive, natural language interface that allows security professionals to interact with their systems as if they were conversing with a colleague. The below diagram illustrates a very high-level picture of the Security Copilot, and how it integrates and works with Microsoft's underlying technologies.
Key Features
- Natural Language Processing: Understands and responds to queries in plain English, making complex security tasks more accessible. For example, we don't have to write KQL queries or PowerShell scripts to retrieve a list of Windows devices that have undergone specific registry changes due to particular malware within a specified time frame.
- Threat Detection: Utilizes advanced algorithms to identify potential threats quickly and accurately.
- Incident Response: Offers step-by-step guidance for addressing and mitigating security incidents.
- Vulnerability Management: Helps prioritize and patch vulnerabilities based on their potential impact.
Key Benefits
The true strength of Microsoft Copilot for Security lies in its ability to process vast amounts of data at machine speed. This capability translates into real-time insights that empower security teams to make informed decisions.
- Efficiency: Reduces the time spent on routine tasks, allowing teams to focus on strategic initiatives.
- Scalability: Adapts to the needs of organizations of all sizes, growing alongside them.
- Accuracy: Minimizes human error by providing consistent, AI-driven analysis.
How to access Microsoft Security Copilot
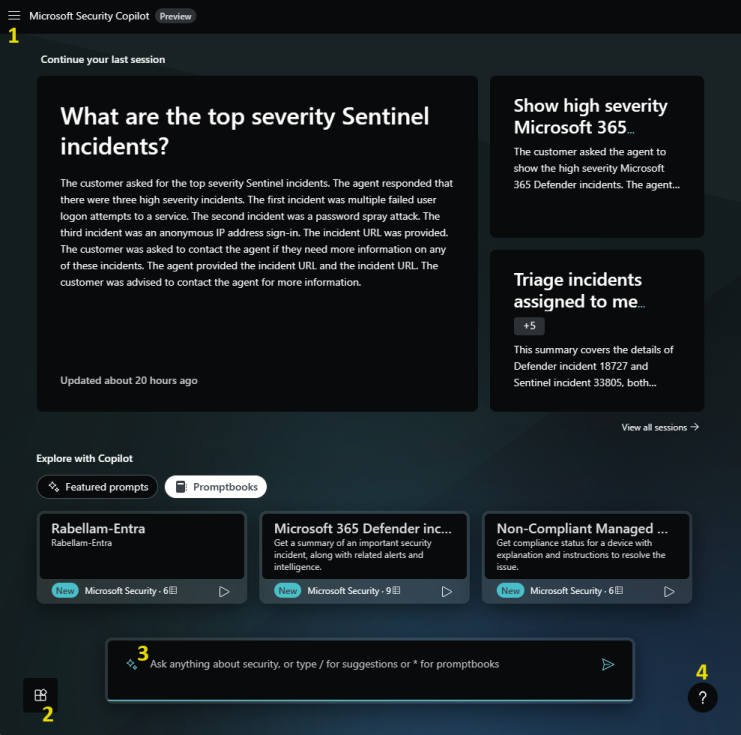
We can access Security Copilot in two ways which is called 'experience' in Microsoft Docs. The Security Copilot offers two types of experiences: standalone and embedded. A license will be required for both experiences.
- Standalone Experience: This is when we access Security Copilot directly, typically through its dedicated URL (https://securitycopilot.microsoft.com). In this mode, we can interact with all the underlying security technologies that Security Copilot offers.
- Embedded Experience: This refers to Security Copilot’s functionality being integrated or “embedded” within other security solution portals. Examples include the Defender portal, Intune portal, Entra portal, etc. In this mode, we’re accessing Security Copilot’s features within the context of these other portals. In the below picture, we can see the Security Copilot has been integrated into the Defender portal.
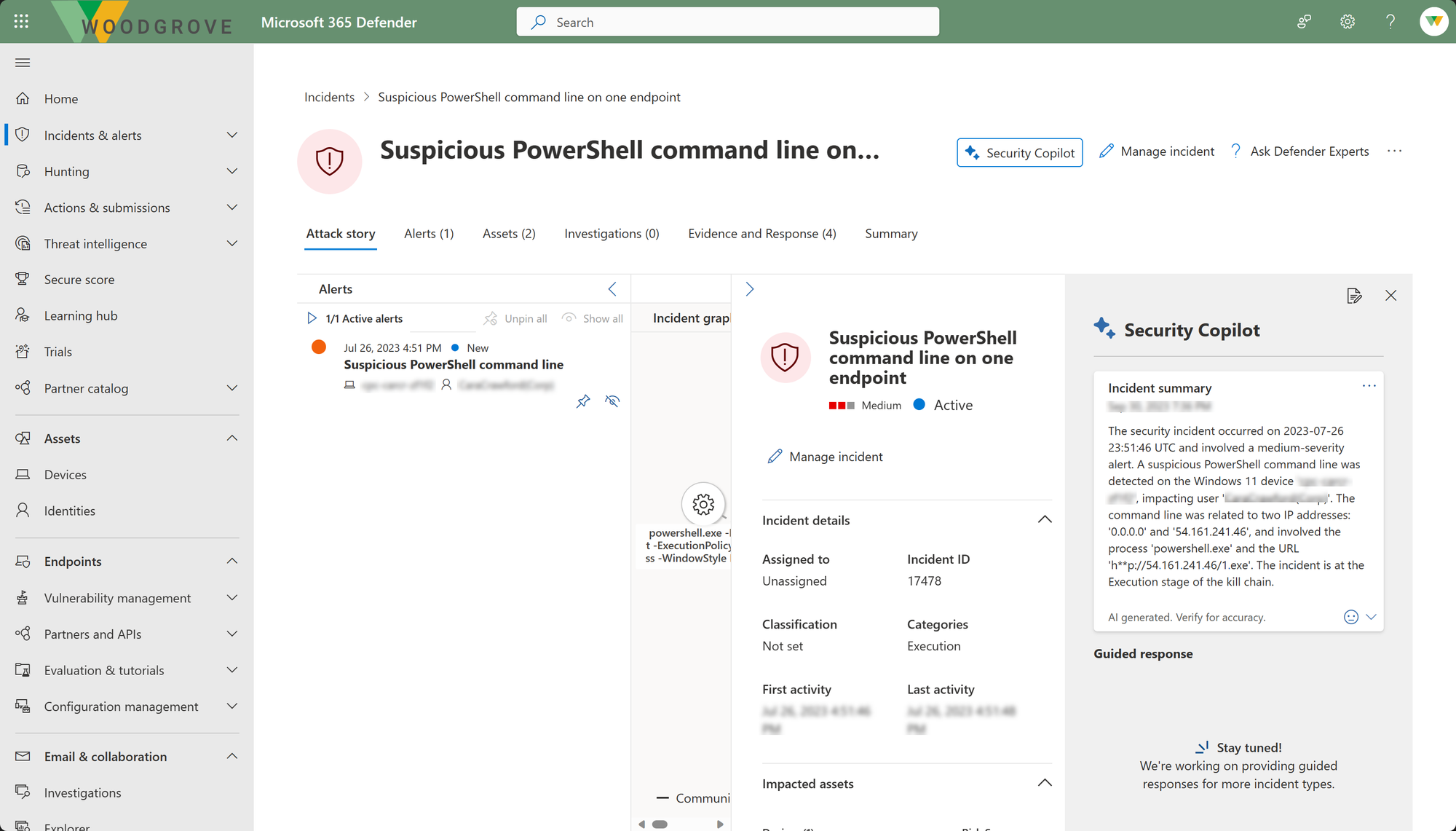
The difference lies in how and where you access Security Copilot’s features. Both experiences provide access to the same security technologies, but the method of access varies. The standalone experience offers a dedicated interface, while the embedded experience provides integrated access to other security solutions.
Security Colipot Terminology
There are a few key terminologies that we need to understand to work with Security Copilot.
- Prompts: Prompts serve as the primary input for Microsoft Security Copilot, enabling it to generate answers that assist you in various security-related tasks. Whether it’s threat detection, risk assessment, or automated investigations, the Copilot relies on well-crafted prompts to provide valuable insights and guidance. Example: “Investigate the compromised server. Provide details on the attacker’s entry point.”
- Promptbooks: Promptbooks are a collection of prompts that have been put together to accomplish specific security-related tasks. Each promptbook requires a specific input (for example, a code snippet or a threat actor name) and then runs a series of prompts in sequence, with one prompt building on the one before it.
- Plugin: Plugin is the primary source of data and intelligence for Security Copilot to work with specific services or address particular security tasks. It is just like connectors in Sentinel, plugins enable seamless integration with services like Defender, Intune, Entra, and many more to extend the capabilities of the platform.
Let's talk more about plugins. To extend the capabilities of Security Copilot, preinstalled plugins are available for Microsoft security services and other commonly used services. Security Copilot uses the on-behalf-of authentication flow to provide access to other Microsoft services that your organization already has access to. Below is a list of preinstalled plugins:
- Microsoft Defender XDR
- Microsoft Sentinel
- Microsoft Intune
- Microsoft Entra
- Microsoft Defender Threat Intelligence
You can also add our own custom plugins, including plugins from OpenAI. External logs can be incorporated into Copilot, and connectivity for third-party tools is facilitated through API integration.
Conclusion
As cyber threats grow more sophisticated, Copilot for Security stands at the forefront of this evolution, offering a glimpse into the future of cybersecurity. It bridges the gap between human expertise and AI capabilities. By harnessing generative AI and MDTI, security professionals can work smarter, respond faster, and stay ahead of cyber threats.
Hope this was helpful, contact me on Twitter @sakaldeep for any queries.