Microsoft Defender AV exclusion list bypass can go undetected by Defender for Endpoint
Microsoft Defender Antivirus exclusion list can be bypassed if the user has the administrative right or the threat actor got administrative access to the device. Microsoft Defender exclusion list from scanning is unprotected and exposed to the end-user. There are two big risks:
Risk1: Privileged users or bad actors can add/remove/modify the Defender AV exclusion list and go undetected by Defender for Endpoint.
Risk2: Any user including bad actors can see the list of exclusions and can plant malware there, and go undetected by Defender for Endpoint.
Disable Exclusion Bypass
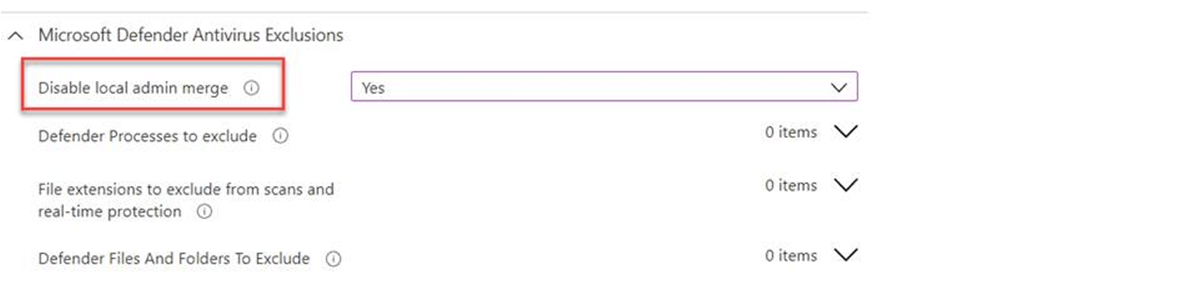
Risk1 can be mitigated by overriding the end-user exclusion list with a centralized exclusion list and that can be achieved from Intune or GPO. In Intune, Endpoint security->Antivirus->Create Policy. In Policy, Microsoft Defender Antivirus Exclusions->Disable local admin merge->Yes. Disable local merge overrides exclusion list added by end-user at the time of scanning, see the official statement from Microsoft below.
Disable local admin merge
This policy setting controls whether or not exclusion list settings configured by a local administrator are merged with managed settings. This setting applies to lists such as threats and exclusions. If you disable or do not configure this setting, unique items defined in preference settings configured by the local administrator will be merged into the resulting effective policy. In the case of conflicts, management settings will override preference settings. If you enable this setting, only items defined by management will be used in the resulting effective policy. Managed settings will override preference settings configured by the local administrator.
In Intune, configure should like below.
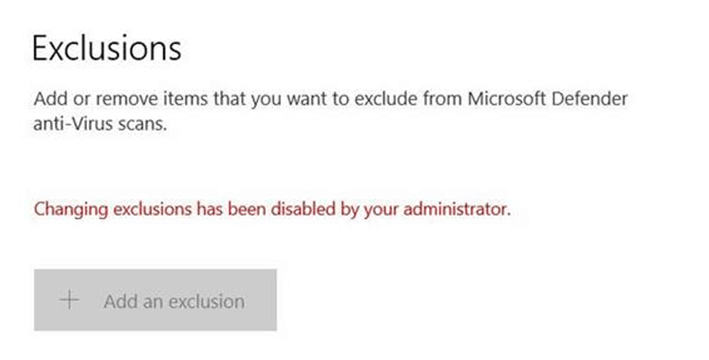
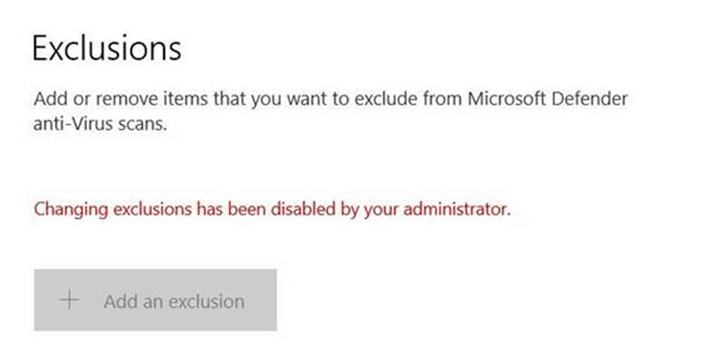
When the Disable local admin merge policy has not applied to the devices then it looks like the below.
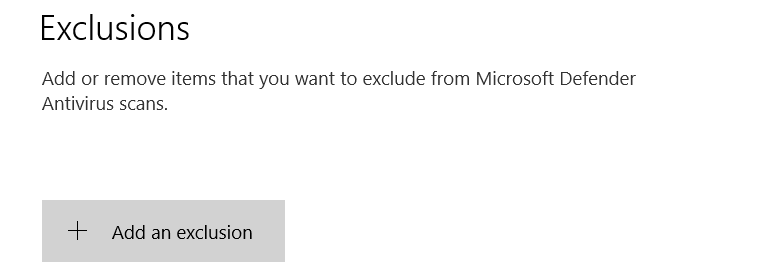
Once the policy will be applied to the devices then it looks like the below. But still, anyone who has access to the devices can see the list of exclusions that are implemented by the admin.
MDE Detection Rule
If you have not applied this policy or a group of devices are excluded from this policy then we can create a detection rule that will generate an alert whenever anyone tries to add/remove/modify the exclusion list. Below is the advance hunting query for the detection rule.
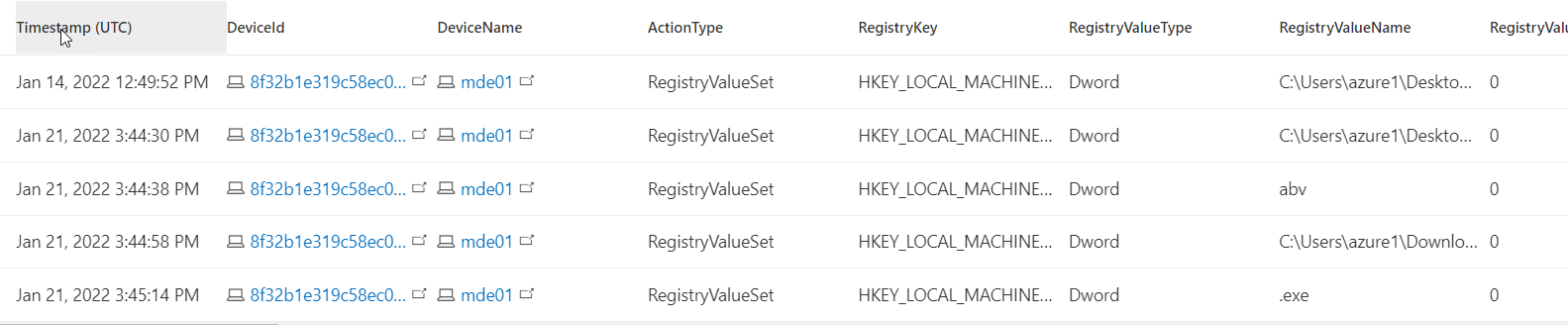
DeviceRegistryEvents
| where ActionType == "RegistryValueSet"
| where RegistryKey startswith 'HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows Defender\\Exclusions' Query output looks like the below.
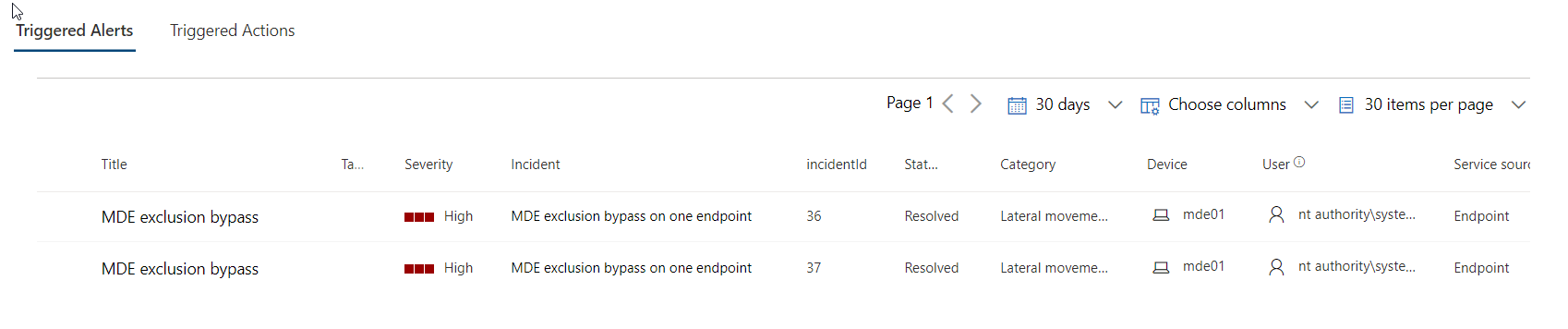
The detection rule will generate alerts like the one below.
Risk2: Currently, there is no solution for this risk and it is a weakness of the Defender AV. As per Microsoft, this risk will be fixed in upcoming updates.
Hope this was helpful, contact me on Twitter @sakaldeep for any queries.